I had a requirement recently where I needed to cut off access to Zoom from my Citrix Virtual Apps and Desktops environment. I’m sure you’re all familiar with Zoom – it saw a rapid explosion in usage once the COVID pandemic took off, and is on the verge of becoming a byword for video calling.
Many security teams, though, don’t share the rosy view of Zoom that most of the world’s user base seem to have. In a lot of enterprises, use of it has been banned outright because of concerns about the code base and privacy. I’m not here to discuss the ins and outs of whether Zoom should be allowed to be used or not – I know of plenty enterprises where it is allowed as well as those where it is banned – but if you do find yourself told to take the ban-hammer to it, this is how you could achieve that.
Naturally the first thought is to simply block access to the Zoom website at the perimeter, but for a variety of reasons, this wasn’t an option where I was – it had to be something done in-session. Group Policy was the only tooling at my disposal, so I had to skin GPOs to meet my needs.
Users generally access Zoom in one of two ways. You are normally sent a link to a Zoom meeting, and from there you can download the Zoom client which installs itself into the user profile, or you can simply join within the browser. The browser option is a bit slippery as it doesn’t appear to use an add-on or extension of any kind – it runs natively in the browser itself.
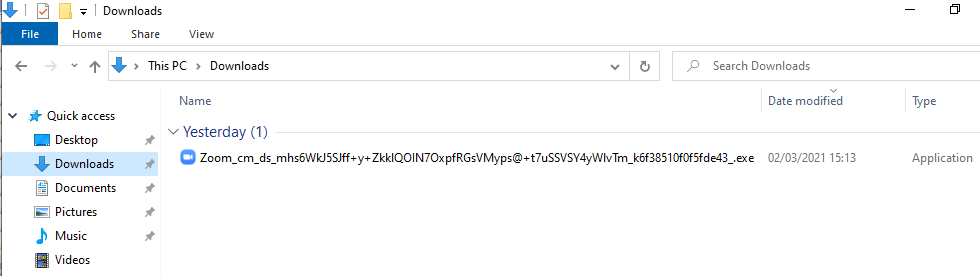
Firstly, let’s deal with the obvious one – blocking the execution of the Zoom installer. It generally saves itself to the user’s Downloads folder with a name of zoom_lotsofrandomtrash.exe as below
For once it’s kind of tricky to use FSLogix App Masking to hide the Zoom executable in this way, as a) you’d have to block the folder potentially, as the filename can change, and b) users could just move it somewhere else. So for once in my life – I’m going to lean away from FSLogix 🙂
AppLocker is the natural next place to land, because we want to be able to block this specific executable from running. In order to block Zoom, first get yourself a copy of the Zoom executable you can use as a reference. You can do this either by trying to join a Zoom meeting, or simply go to https://zoom.us/download
Next, switch over to your Group Policy Management Console and fire up a new policy to apply to your targets. Go into Computer Config | Policies | Windows Settings | Security Settings | Application Control Policies | AppLocker
Note – this article suggests setting up AppLocker in such a way so that only the Zoom executables are blocked. In an enterprise environment, it would be better to block in a “whitelisting” rather than a “blacklisting” capacity, but setting up in this way requires a degree of due diligence to be performed first. For an in-depth discussion of AppLocker and other whitelisting technologies best practices, consult the Microsoft documentation (or read this article – which may have someone else’s name on it but was actually written by my good self).
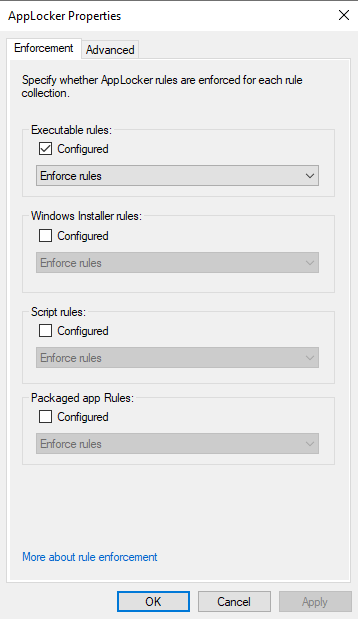
Firstly, right-click on the AppLocker node, choose Properties, and switch the Executable Rules setting to “Enforce rules” as below
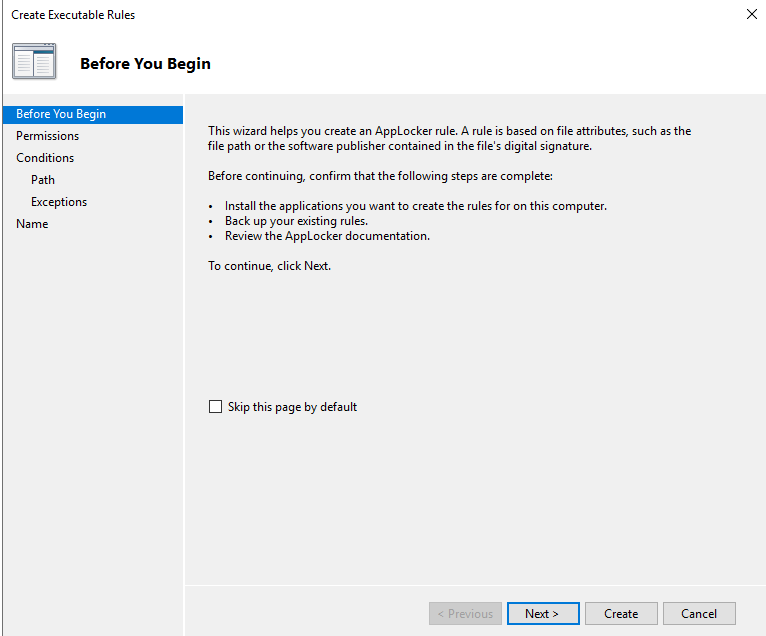
Next, set up a rule which will allow the Everyone group to run all files, with an exception to disallow the Zoom executables. Click Create New Rule in the Executables section
Click Next
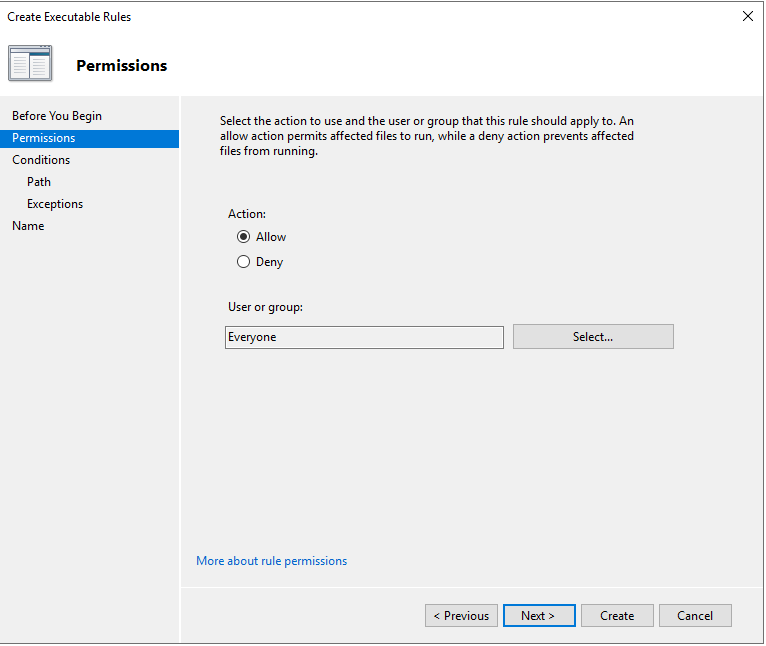
Set the Action to Allow for Everyone as above
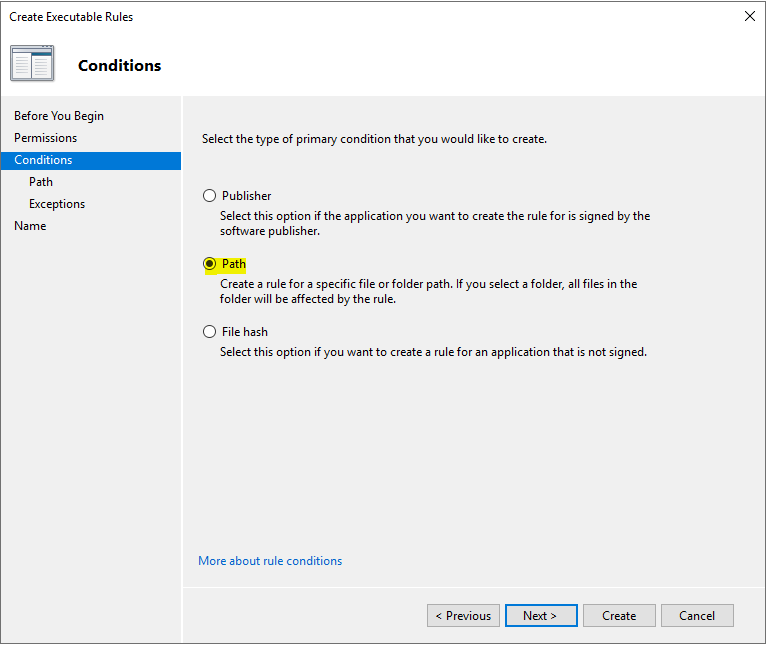
Create a Path rule
Add * as the path so that all executable content is allowed
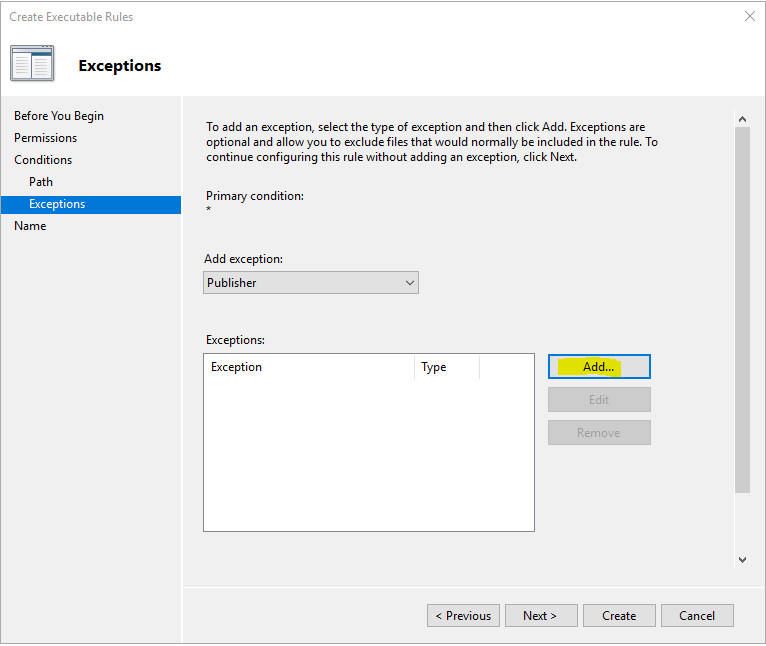
Click Add to put in an exception
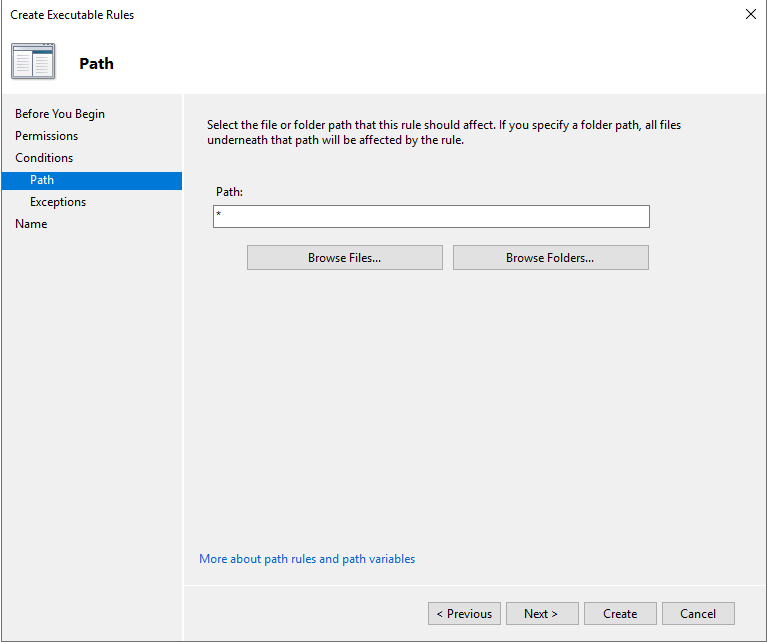
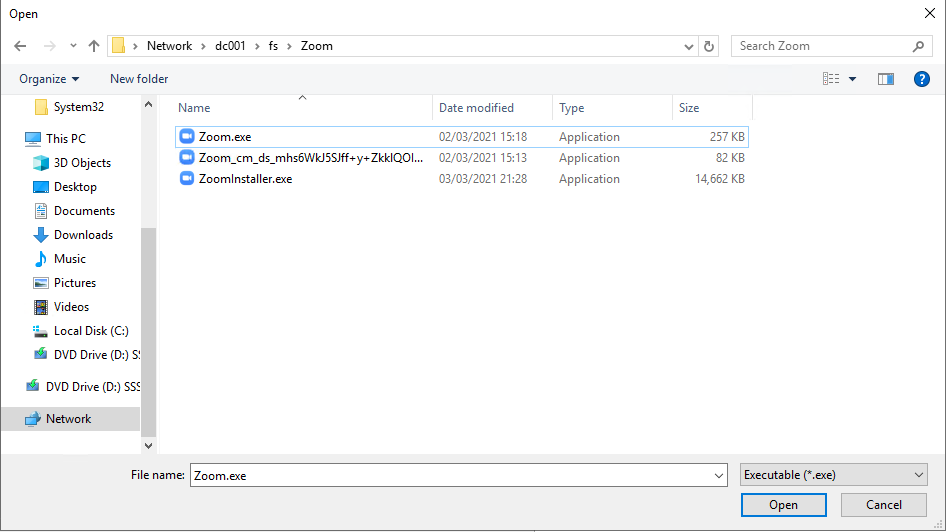
Click Browse to find the reference file you saved earlier
Locate your Zoom executable and click Open

Move the slider up until it reaches Publisher as shown above, and click OK
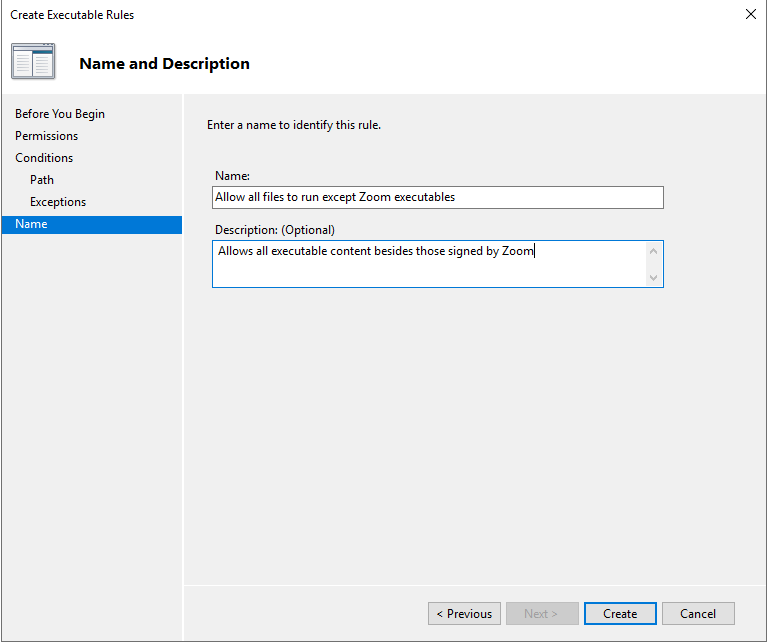
Give the rule a Name and Description, and click Create
Now before you test this, there are two more vital things you will need to do.
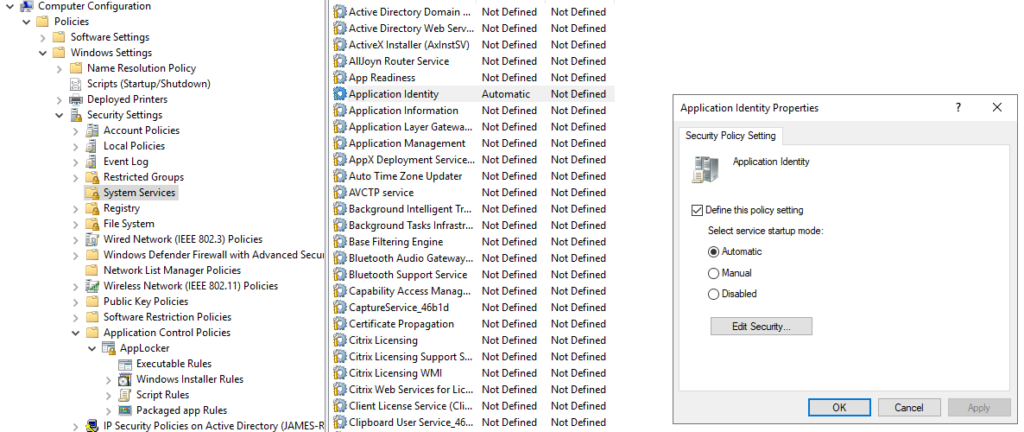
Firstly, AppLocker doesn’t work unless the Application Identity service on your targets is running. Best way to configure this is through Group Policy – but bizarrely, you can’t use Group Policy Preferences Services to do this (it errors out with access denied, for some reason). You will have to use an old-fashioned policy to enable it in Computer Config | Policies | Windows Settings | Security Settings | System Services and configure the Application Identity service as below
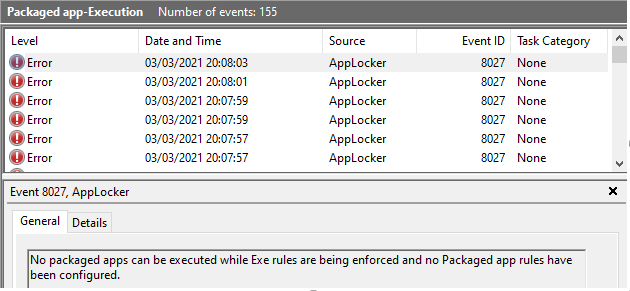
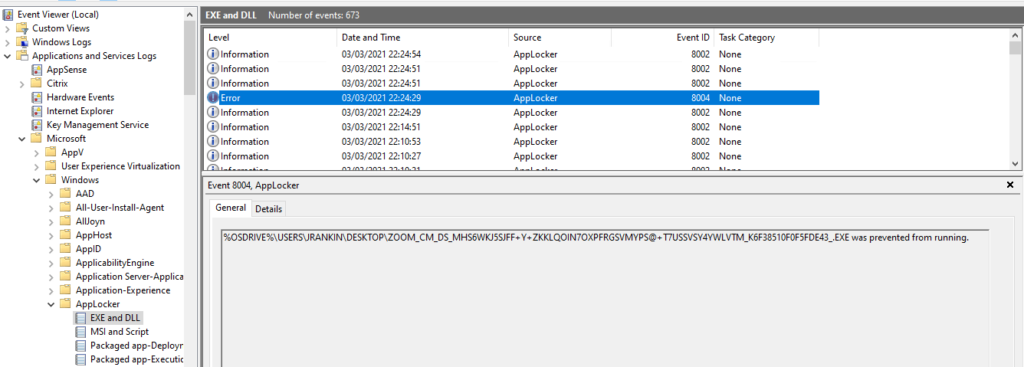
Secondly, when you configure AppLocker Executable Rules to be Enforced, this also starts blocking Packaged Apps (UWP apps), even if you haven’t configured the enforcement. And this will include such vital things as the Start Menu, Settings app, etc.! You will be able to tell if you’ve forgotten to do this because the AppLocker event log will be full of the below error (and nothing will work)
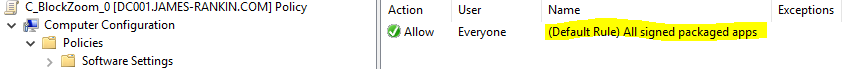
To avoid this, right-click on the Packaged App Rules node inside of your AppLocker policy and choose Create Default Rules
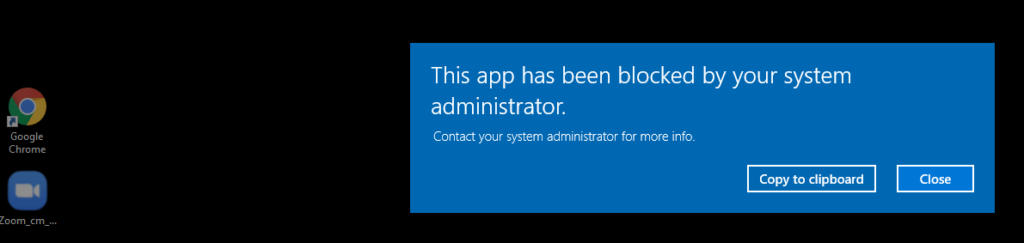
Once this is done, you should be able to propagate this policy to your target devices and find that whilst everything can execute, any executables signed by the Zoom publisher are now blocked from running altogether.
So we’ve blocked the executables, but how can we block users from running it in the browser?
Well, this should be fairly simple (not as simple as blocking at the perimeter, but simple enough) because all the Zoom meeting links point to a https://zoom.us address.
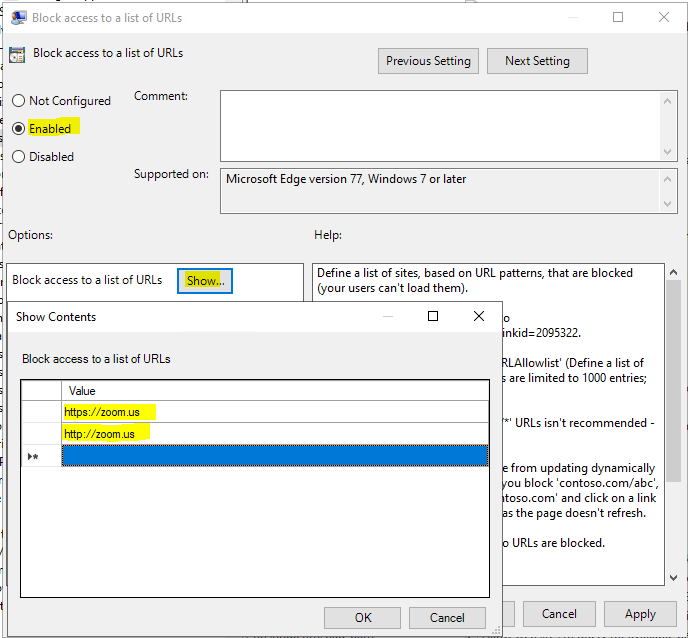
For Edge Chromium and Chrome, we can simply block this by using the appropriate GPOs. For Chrome:-
Computer/User Config | Policies | Admin Templates | Google | Google Chrome | Block access to a list of URLs
For Edge Chromium, use Computer/User Config | Policies | Admin Templates | Microsoft Edge | Block access to a list of URLs
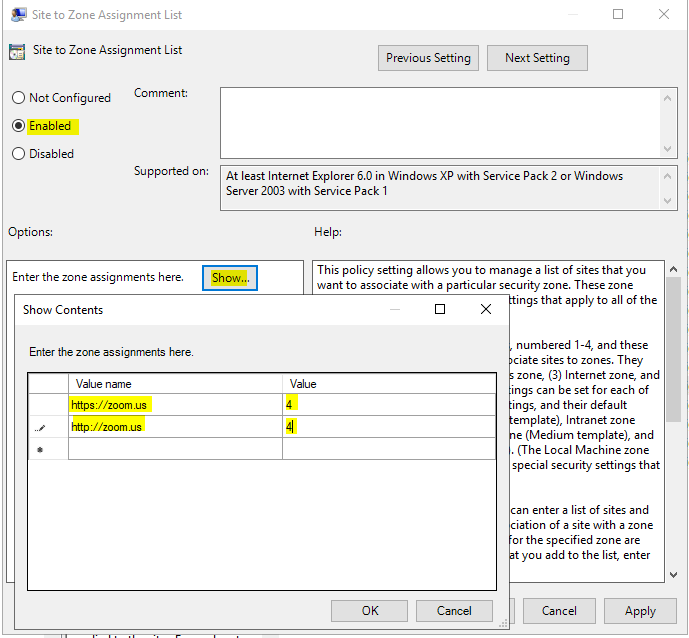
Internet Explorer (should for some reason you still be using it or have it available – why not uninstall it?) is slightly more troublesome. Best way to block the site is to add it to the Restricted Sites list via GPO, which is found at Computer/User Config | Policies | Admin Templates | Internet Explorer | Internet Control Panel | Security Page | Site to zone assignment list
A value of 4 puts the sites into the Restricted Sites zone, which should normally be pretty locked down.
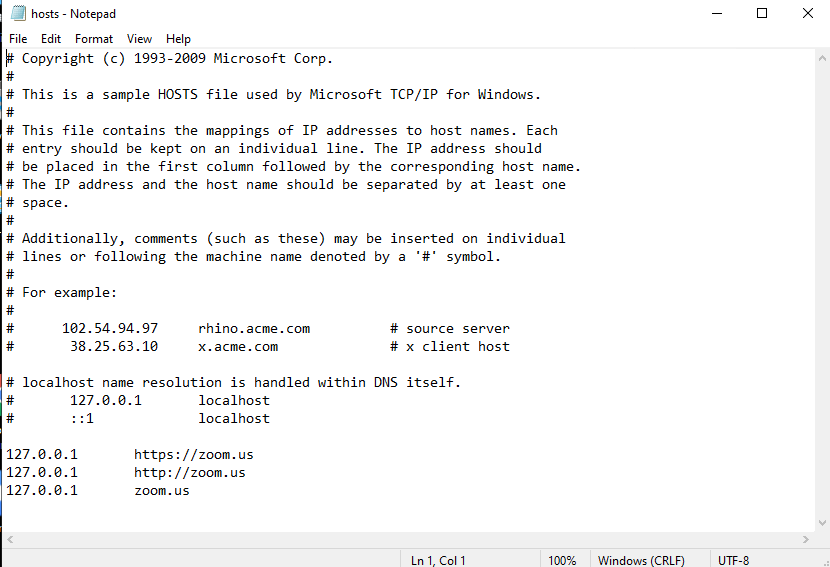
Of course, there are always other ways through things – the users could use another browser like Firefox or Opera, the Restricted Sites settings could be too lenient, they could access from a console session or another application. In order to lock these down, it is probably worth going the full hog for a belt and braces approach and remembering the old trusty hosts file can be leveraged.
Open up the hosts file from c:\windows\system32\drivers\etc with admin privileges, and add these lines to the file
127.0.0.1 https://zoom.us
127.0.0.1 http://zoom.us
127.0.0.1 zoom.uswhich should leave your hosts file looking something like this
You could deploy this out through Group Policy as well if you so wished, using a Group Policy Preferences Files action. Once it is on the targets, this gives us a final layer of coverage to prevent access to the Zoom site that the user needs to access to run meetings within the browser.
So when our users try to backdoor their way into browser-based Zoom by using the web links, they should now find themselves frustrated
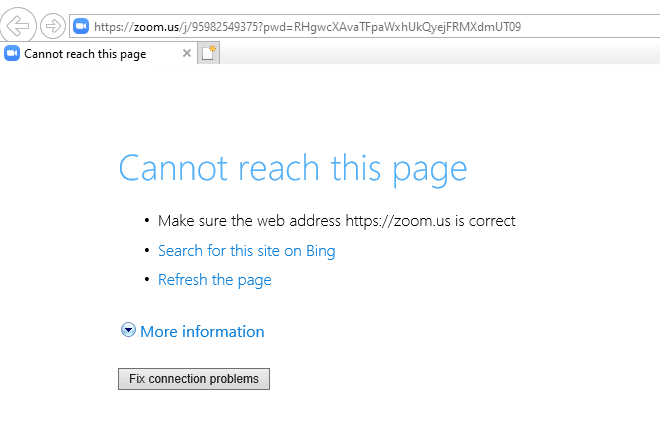
In Internet Explorer:-
(Incidentally, without the hosts file in play, IE would display like this, assuming the Restricted Sites zone was in the default configuration)
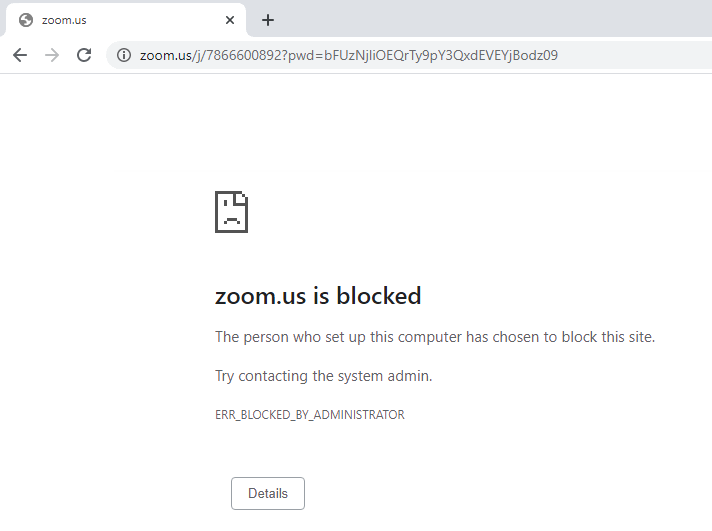
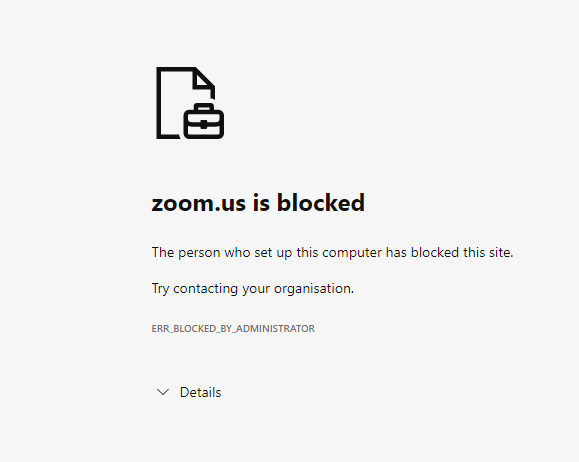
In Chrome and Edge Chromium, you get this error
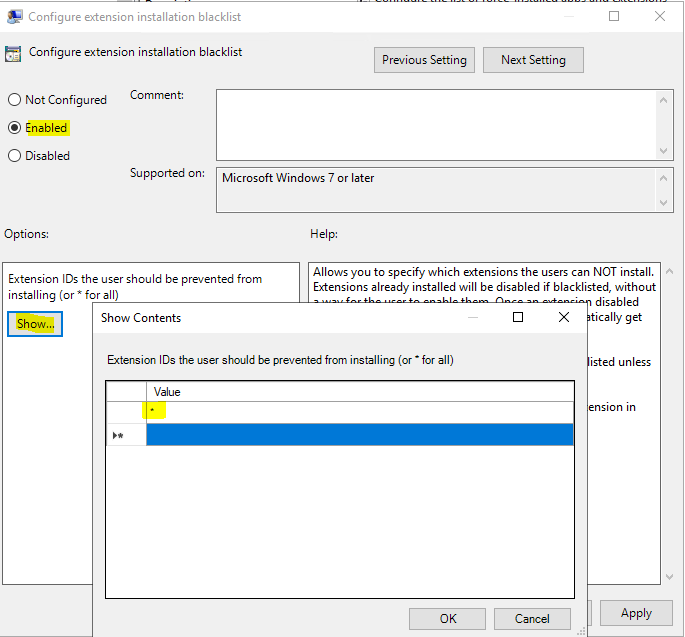
All that remains is to ensure that the users can’t do anything with the Chrome extensions. You can restrict the extensions using GPOs as well – I normally add all Chrome extensions to the blacklist under Computer/User Config | Policies | Admin Templates | Google | Google Chrome | Extensions | Configure extension installation blacklist, with a value of * as below. You can then add only the extensions you want to allow to the Configure extension installation whitelist value, making sure to omit the Zoom extension ids from the whitelist policy.
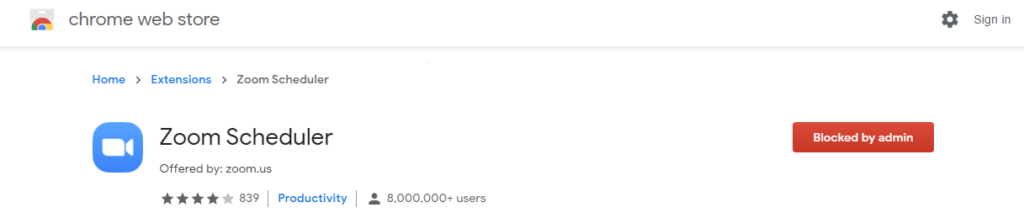
If the users try to install it, they will see this
Edge Chromium doesn’t have the same extensions whitelist and blacklist policies, but neither does it yet have a Zoom extension, as far as I am aware. If you have Firefox, you need to block the add-on as well. However, even if users manage to install the extensions and/or add-ons, the policies we configured earlier should still prevent them from joining meetings, so we are again simply using this to add a multi-layered solution.
So, if you find yourself in the same boat as me, and forced to come up with a way to use GPOs to restrict access to Zoom, this offers you a way to cut the users off without too much trouble. As I said earlier, this is a very permissive set of AppLocker policies and really if you are going to implement AppLocker, you should take the time to set it up properly and drastically improve your security posture, but for blocking Zoom, it works just fine.
Stay tuned for some upcoming cool stuff to help you manage Teams (and your general Citrix environment) better – all things being well, it should be dropping by the end of the week. Also I should have a few videos to put out – I need to, now that thanks to everyone in the EUC community I’ve cracked the 1,000 subscriber mark, I am eternally grateful (and also to Rory Monaghan for driving the subs to me).
![]()