It’s time for a product review and a look into the Active Directory security space. Over the last couple of weeks I have been working with a product called UserLock from a company called IS Decisions. The primary focus of the product is around managing and securing logons to AD.
Background
Security is pretty big these days. I hosted a webinar with fellow CTP Dave Brett yesterday where we talked about how administrators must now tread a fine line between balancing performance against the need to provide adequate security. Not surprisingly, securing access to Active Directory is high on the list of priorities, as a huge percentage of enterprises rely on AD to underpin their applications and services. UserLock is a product aimed at improving the management and security of an AD implementation.
Setup – server
UserLock is pretty straightforward to get up and running. The software comes with an unlimited one-month evaluation license. The installer runs through quickly and easily.
One point worth making is that by default the software will install with a Microsoft Access database (which feels a little bit unusual given the predilection of vendors to use SQL Express), which to be fair keeps the installer lightweight (although this is scheduled to be replaced by SQLite in an upcoming release). Once installed, you can then configure the product to point at a proper SQL Server, SQL Express or MySQL instance for production deployments and take advantage of the proper resiliency and performance these databases provide. There is a little bit of manual intervention required in order to achieve this, however, as you must create the empty database prior to making the connection. It would be nice to see this built into the installer perhaps, or maybe even provide some scripts to run to achieve this, but it is not a show-stopper and should not present much of an issue for the administrator.
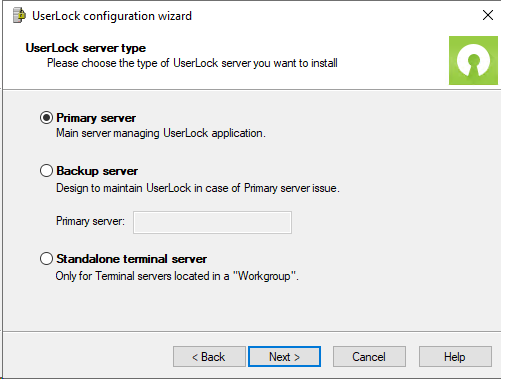
Once the installer is completed a configuration wizard runs that allows you to select whether the server you are installing is in primary, backup or standalone mode.
The UserLock software performs a check for any primary server defined and if this is unavailable, will fail over to a backup server. Unfortunately this cannot be integrated with a load balancer, for instance, as the UserLock agent does not use Registry items or filesystem config settings to direct its traffic. This is not a huge issue but in environments where it is standard practice to proxy applications through load balancers may be a consideration to be aware of.
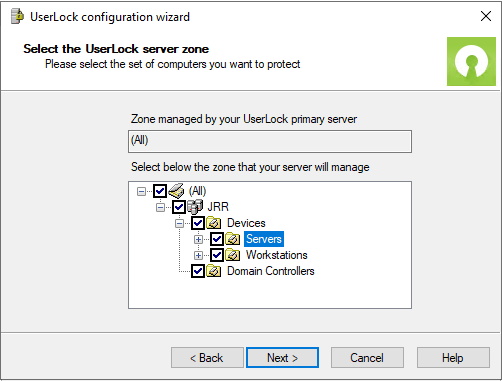
You can furthermore select a “zone” within your AD domain(s) or forest(s), allowing you to scope the management of devices to particular areas if necessary.
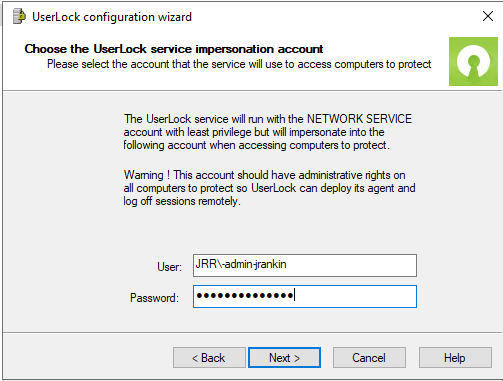
A service account with administrative access to the managed devices is required.
This is all that is required from the server perspective – so in summary, very quick and pain-free. It’s worth noting that no changes to AD or AD schema are required either, so this is also good from a perspective of change management.
Setup – client
The next step is to distribute the UserLock agent to your target devices. You can do this from the console, or alternatively you can download the MSI and distribute it to target endpoints using a technology like, for instance, System Center Configuration Manager. The agent is pretty lightweight and simply registers as a Windows service from a source executable in c:\windows\syswow64.
The targets require the Remote Registry service to be enabled and Windows Firewall exceptions for File and Printer Sharing (including File and Printer Sharing Over SMBDirect) . In high-security environments this may present a challenge but if the access can be restricted to the specified UserLock server(s) then it should be doable.
I quite like that when deploying from the console, if an error occurs, there is a “Fix it for me” option along with informational feedback about what is causing the issue.
There is an “Automatic Mode” but use this with care otherwise it will attempt to perform deployment to every possible target it can see.
Once your endpoints have the agent successfully installed, they will show as successful in the console
Setup – users
Next, you need to configure user accounts to be managed on the devices where UserLock is installed. It would be handy if there was an option here for “manage all users on device X”, which would cut down the setup time if you were simply looking to protect high-value assets (such as Privileged Access Workstations, or PAWs).
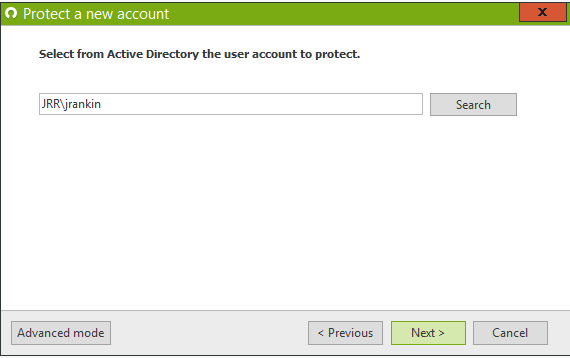
UserLock calls these managed accounts “protected”. Protecting an account is as simple as adding them via a wizard. You don’t have to do accounts individually – you can add Active Directory groups or Organizational Units too.
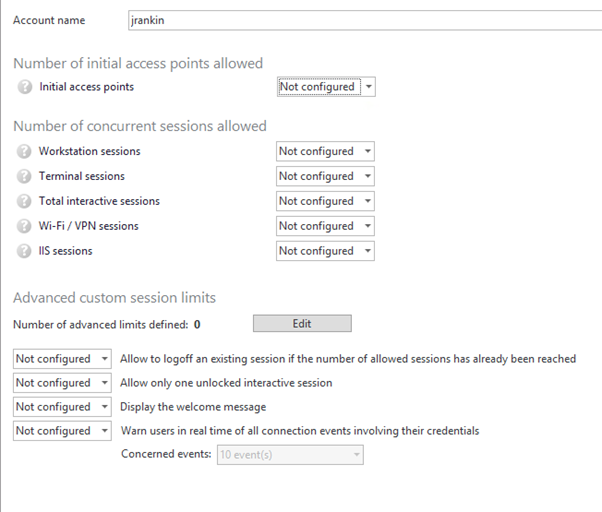
Once you have added the required users into the scope of protection, you can see that you have a multitude of options as to how you can restrict them. This is where UserLock has a lot of configurable options that offer a wide variety of assistance with different scenarios. You can configure device restrictions, time restrictions, geolocation restrictions – there are a lot of settings you can mix and match here, which gives you a powerful toolset to leverage.
One gripe I do have here is that the console is quite grey in colour and a few settings are actually “available but unconfigured” but actually look like they are “greyed-out and unavailable”. This is a minor thing but I did find it a little confusing, a stronger colour scheme would help. That aside, though, I have to mention that I find the UserLock console easy to use and familiar – it appears to be based on the same interface as Server Manager so that’s why it feels recognisable.
But from a feature perspective, you can get very granular with how you want to apply user security settings. This gives the administrator a whole lot of power that they can use to create custom policies beyond what is natively capable in Active Directory.
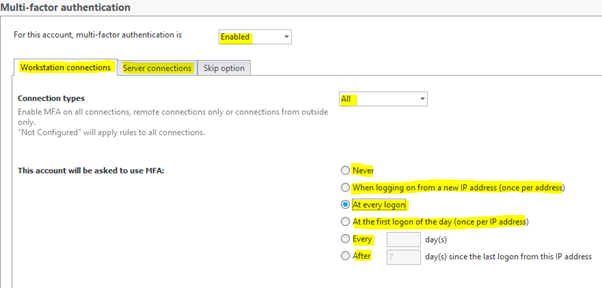
Multi-factor authentication
Rather than look through each feature, which would result in a very long review, let’s look at one that we’re specifically interested in – MFA for endpoints.
MFA for endpoints is difficult to put together without third-party software, particularly as Microsoft seem set on pushing Windows Hello rather than extend their own services towards endpoint logons.
One thing I do have to say about UserLock is that setting up MFA for endpoints is *very* easy. I’ve used other products where there has been a long process before MFA for endpoints would work, but I found UserLock really straightforward in this respect.
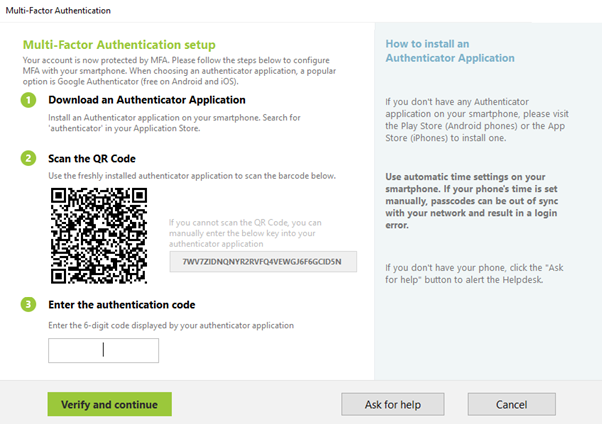
On the latest version of Windows 10, my test user is prompted to install an authentication app and scan the QR code.
Once this is done, they enter the code from the authenticator app and continue.
At subsequent logons where MFA is required, they are simply presented with this dialog.
The authenticator service can be anything that can scan a QR code and use TOTP. I used the Microsoft Authenticator service, but there are many to choose from, including things like Sophos, LastPass, Authy and Yubico. Yubikey and Token2 are two of the hardware-based devices it supports, which offers alternative styles of authentication, and it is encouraging to see such a broad range of products that are compatible with the software.
There currently isn’t the option to use the pop-up “Approve request” as a push notification from the authenticator service rather than opening the app and entering the code, but this is on the UserLock roadmap and will help speed up users logging on via MFA.
I also wanted to test this using a Citrix Virtual Apps logon, to see if it works in RDSH environments, which are of particular interest to me as an EUC-focused technologist.
I was impressed to see that the product works for users out-of-the-box on Citrix Virtual Apps running on a Windows Server 2019 instance, which I found really good. There was no further configuration required on the UserLock or Citrix side.
I could not verify this as I am unable to attend any customers because of the COVID-19 lockdown, but I am informed that UserLock will also support MFA when logging in via an NFC card rather than using standard Windows credentials (and even using Windows Hello, for that matter). This is also really good as I know of use cases where clients wish to use NFC logons in conjunction with endpoint MFA.
There are no fallback options currently available for the MFA (for instance, to offer a “call my phone” in the event the authenticator service is down). This is being looked at as a roadmap feature.
The user can also “ask for help” which allows the administrator to be notified at the console or via email and take some corrective action (such as resetting MFA, or turning it off). This functionality is handy but a little limited currently, although you can send the notifications through to other apps (such as Slack, for instance).
Other points
During my use of the software, here are some other observations I made.
- There is a web console available as well as the full console, so you can provide access to other delegated sets of administrators. Delegation of security roles is fully AD-integrated.
- There is a lot of reporting available, so you can extract data to aid with security logging and tracking. You can also configure a webhook to grab the data for an SIEM tool.
- Service errors log out to a file called servicelog.txt on the server end, so you can check there for more advanced troubleshooting.
- You can customize the branding, which is essential for many enterprises.
- The software will also support MacOS endpoints, which I couldn’t test (because I don’t have any Mac devices!), but other reviews indicate that it works for these targets.
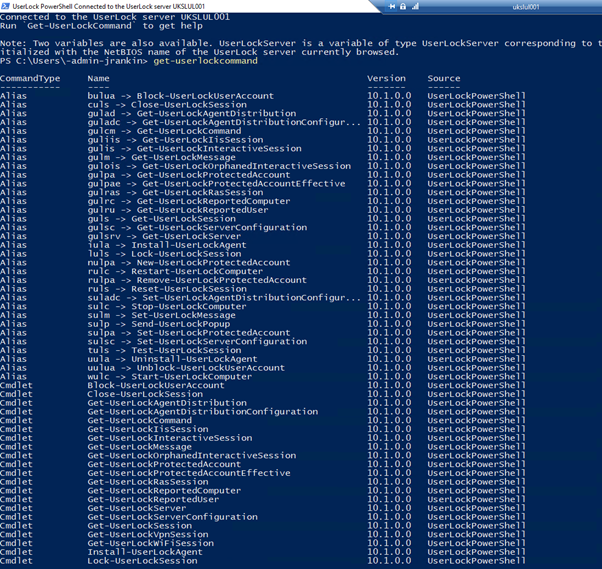
- The software has its own PowerShell implementation, which will be very useful to those who rely on PowerShell to automate and manage their estates.
Verdict
I’ve only really scratched the surface of what can be done with UserLock. It certainly seems to offer a lot of functionality related to securing AD and user accounts, and this feels like a good thing. It is very interesting that you can go to work on Wifi and VPN logons, IIS logons, and there is a lot of tooling that could help out with particular use cases.
I found the initial setup very easy and particularly the MFA setup was noticeably painless as well. The console was easy to navigate, and the functionality easily located. There was no need to tinker with web services or – in particular – certificates in order to enable the functionality.
There are a couple of limitations that spring out – obviously the lack of MFA options rather than just the code response would be nice to see addressed, and maybe some more wizard-driven options around the setup of a production SQL database would be good in live enviroments.
Overall, I feel like this is a product with a good deal of potential.
As GDPR comes along and security moves up the priority lists again – particularly with the mass of users now operating from home during the COVID-19 outbreak – it may well be an essential piece of tooling for many estates. A lot, though, depends on the price point that it retails at against the use case you have – UserLock is licensed concurrently (and perpetually, which is a nice change from the usual) at a base price of 12 Euros, but that, as with every software purchase, comes down as the license volume increases. In summary, though, I think this is an interesting product that is easy to get familiar with and that offers a lot of useful tooling for environments where security is on the agenda. I have a personal interest in seeing what this can offer to environments where PAWs (Privileged Access Workstations) are being used, and think that it might do well in bringing value add to those solutions by the controls it can offer over and above those available natively in AD.





One comment