There was a lot of noise about this issue lately – hopefully this will help some people out!
So, I remember seeing a few weeks ago a lot of chatter in Slack and Microsoft forums about FSLogix Profile Containers customers having issues with intermittent application of user group policies. A lot of people seemed to report it was on the latest version that this problem existed, and moving down to an older version (7217 if I recall correctly) fixed it for some. Others still reported seeing the problem on whatever version they used, and whether this was on any Windows operating system.
Naturally, as this problem didn’t appear to be affecting me, I put it down to something in their environments that I didn’t have in mine (selfish, I know, but we’re all a bit busy recently). However, when I was doing testing for a new build of our Citrix Virtual Apps image, I noticed that it was happening to me too.
The problem
The first logon always seems to be fine, when a user creates their profile in the VHD file store. However at second logon, I noticed that our Start Menu layout (partially locked, applied via GPO) was missing, and more worryingly, restrictions like command prompt and registry editing had been lifted. Knowing that this would create a security issue straight away, we did some digging, and found the following in the event logs:-
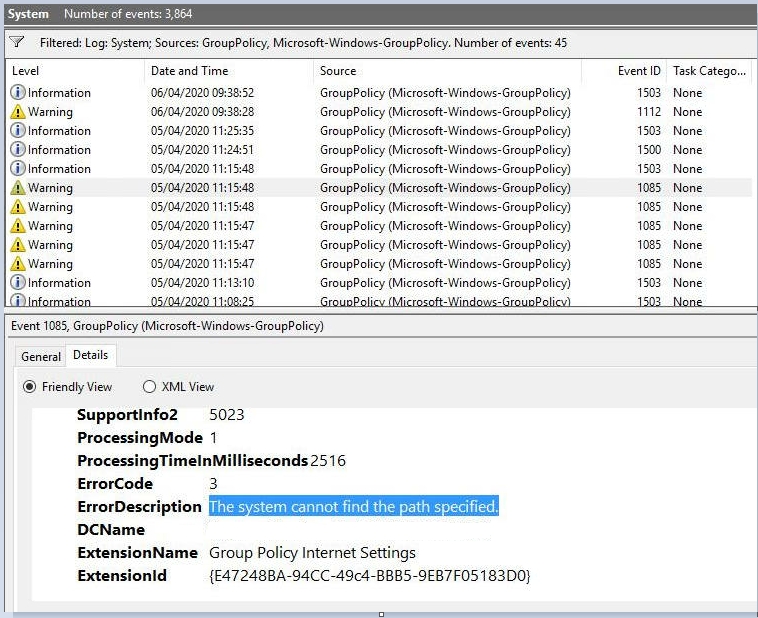
A number of client-side extensions were reporting the same error. What was noticeable is that user GPO processing was completing in 2 seconds, as opposed to a more normal time of 30 seconds (yes, this environment hasn’t had my optimization skills fully let loose on it yet!)
The odd thing was, though, that the system appeared to be contacting the domain controller absolutely perfectly. It got a response, it wasn’t on a slow link, it knew the GPOs that it had to apply for the user, yet when it came to process the CSEs – it couldn’t find them. We checked SYSVOL, we checked domain controllers for errors – everything appeared to be working fine.
Initially we were thrown a red herring when we uninstalled FSLogix and the problem persisted. Using Citrix UPM gave the same results. So we were convinced it was something within the new build – the fact that it didn’t seem to happen in our production environment only added to this feeling.
However, when we took the existing production build and added it to the testing environment and saw the same errors again, we knew there was something really odd going on – so at this point we engaged with Microsoft to do some advanced troubleshooting.
Group Policy caching
It turns out that the issue has its roots in Group Policy caching. This was introduced from Windows 8.1 onwards and is a way to make foreground synchronous processing process more quickly. It doesn’t allow GPO processing to be done when domain controllers are unavailable and/or the machine is off the network – the only way to do that, as far as I know, is to adopt something like PolicyPak which has an “offline reinforcement” setting (there you go Jeremy, saves you emailing me ;-)) For more info about synchronous and asynchronous processing, read this article.
Group Policy caching is normally enabled by default, but only for clients. To enable it for server operating systems (such as we are often using in Citrix Virtual Apps environments), you need to enable the following policy – Computer Config | Admin Templates | System | Group Policy | Enable Group Policy caching for servers

There is also a setting in the same folder called Configure Group Policy Caching, but this seems to only apply to clients where it should be on by default anyway. Don’t get the two mixed up.
As I said this only applies to foreground synchronous processing, which on a server operating system would be done at every logon unless you have enabled “Allow asynchronous user Group Policy processing when logging on through Remote Desktop Services” (obviously in the Citrix world I’m assuming all of your servers are RDSH!) But even if you have enabled this, if you use a client-side extension such as Folder Redirection, you will get forced into foreground synchronous at logon if the CSE in question has changed. Or, if you have the “Always wait for the network at computer startup and logon” policy set to Enabled, then every logon will always be foreground synchronous. As I said, more information about the mysteries of processing modes is in the previous article linked earlier.
So once a user logs on, as soon as a background refresh is completed, GPOs are now cached down onto the device (for Computer Config settings) or into the user profile (for User Config settings). So next time the user logs on in foreground synchronous mode, if possible, the cached GPOs will be used – potentially making the logon time faster (which everyone knows I am keen on). Having to fetch hundreds of GPOs from the domain controller could potentially cause a bottleneck here.
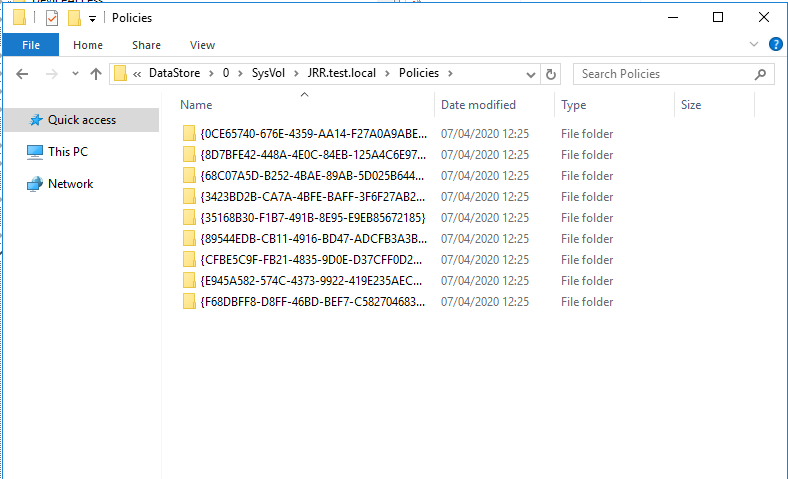
When the user policies are cached, they are written to %LOCALAPPDATA%\GroupPolicy\DataStore\0\SysVol\domainname\Policies
There is, however, also a Registry key that backs up this cache and tells the system where to go to fetch these user policies. This sits in HKLM, which was a bit of a surprise. The key is HKLM\Software\Microsoft\Windows\CurrentVersion\Group Policy\DataStore\[USERSID]\0, and contains a number of numbered subkeys. Each of these subkeys has a value called FileSysPath which tells it where to find the cached policies.
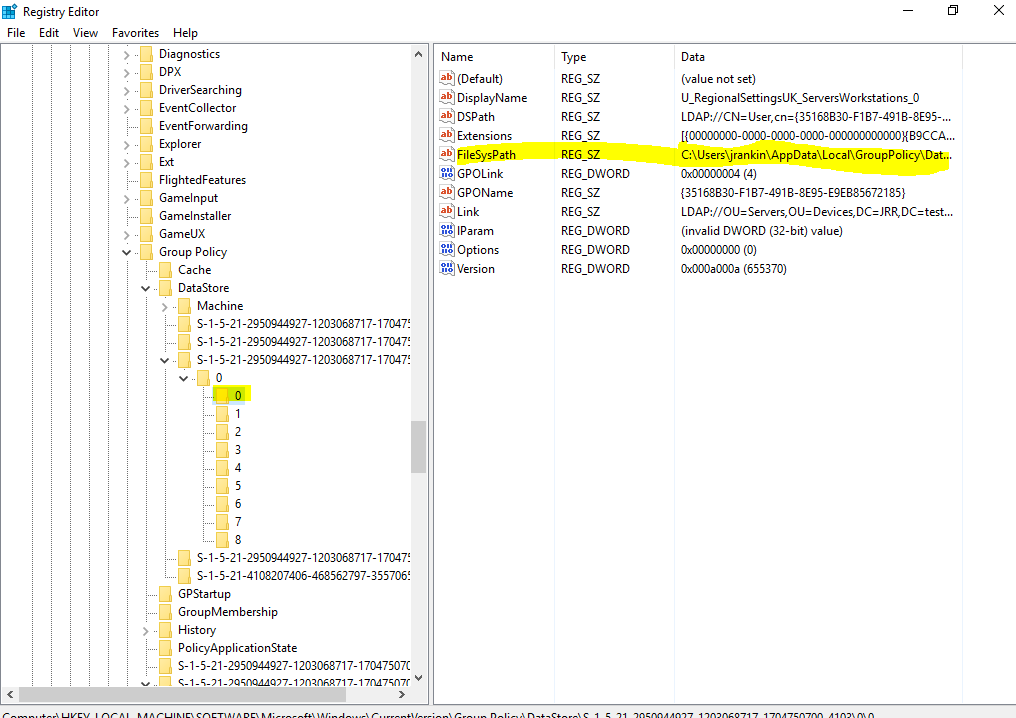
All sounds pretty straightforward – this local cache is used to speed up your logon a bit. The weird bit is the use of an HKLM entry to point it to the files – user profile is normally loaded before user GPOs are processed so I don’t know why this can’t be read from HKCU.
FSLogix exclusions
However, most of use us the FSLogix redirections.xml in conjunction with Profile Containers to avoid filling our profiles full of bloated crap and wasting storage. And most of us use the community redirections.xml files as a starting point to take advantage of the hard work done by others in discovering files and folders that are extraneous. And (you can see where this is going), those community XML files often contain the following entry:-

That’s the kicker – when the user logs in for the second time, Group Policy caching believes it has a local cached copy of the GPO files (because of the FileSysPath entry in HKLM). It then tries to access them, but because they’re excluded from the FSLogix Profile Container, they can’t be found (hence the error of “cannot find the path specified”). The GPOs can’t be processed, the logon finishes, no Registry values exist for your GPOs, and you’re left in a bad state.
Resolution
So the best way to resolve this is, simply, remove the exclusion from the FSLogix redirections.xml file. It’s not a huge folder (8KB in my lab, 3MB in a large enterprise), so leave it in there.
The reason the problem is quite intermittent is because users would have to hit the same server again that they logged on to before to see the problem. When we went back through our SIEM, we found instances of it going back a long time, but clearly users had not noticed. So it was only when we were on a limited number of test servers that we actively spotted the problem, which made us think it was a build issue initially.
Some people have asked “why not turn off Group Policy Caching via GPO?” Well you can, but I would sooner have it on and take the potential benefits of speeding up your logon a bit, especially if you are tied to foreground synchronous mode.
You could also drop the HKLM [USERSID] folders at logoff, but again, you’d be fixing the issue but basically disabling caching. In cloud environments particularly, reducing LDAP calls is maybe a good thing.
It’s also possible this problem affects Citrix UPM as well (UPM also excludes the GPO cache folder) – it may also affect other profile management products too. We certainly saw it with UPM in testing but have not tried at scale (because we’re not keen on UPM any more)
If you do get users with this issue, you can take the following actions:-
- Remove the APPDATA\Local\GroupPolicy exclusions from your redirections file and deploy it
- Remove the HKLM entries for the affected users from any servers you find them on
- If you don’t want to give the user a new profile (who does?), have them log back on, run a gpupdate (so that their local cache is created), then log back in again and everything should be golden
This should sort out the issue and in our testing it does not reoccur.
An interesting observation about this, however, is that if a user logs in to a machine and creates the HKLM SID entry, and then their profile is deleted – the next time they log in their GPOs will fail to apply, because it will look in the local profile for them and they will not be there (because it has only just been created). This is rather annoying and leads me to believe that in environments where a profile management tool is used there should be some way of clearing these up. If a user logs on to 500 different XenApp servers and then you have to delete the central copy of their profile – you would need to remove the Registry key from 500 individual servers before the user could log on to them successfully and get all their GPOs applied. I think it would very prudent to clear this key at boot, and/or clear it within your golden image.
Thinking about the issue, we already know that there is a Registry key in HKLM that is user-specific (HKLM\Software\Microsoft\Windows NT\CurrentVersion\ProfileList\[SID]. FSLogix deals with this by using .reg files from %LOCALAPPDATA%\FSLogix to insert the data in here on the fly (see image below).
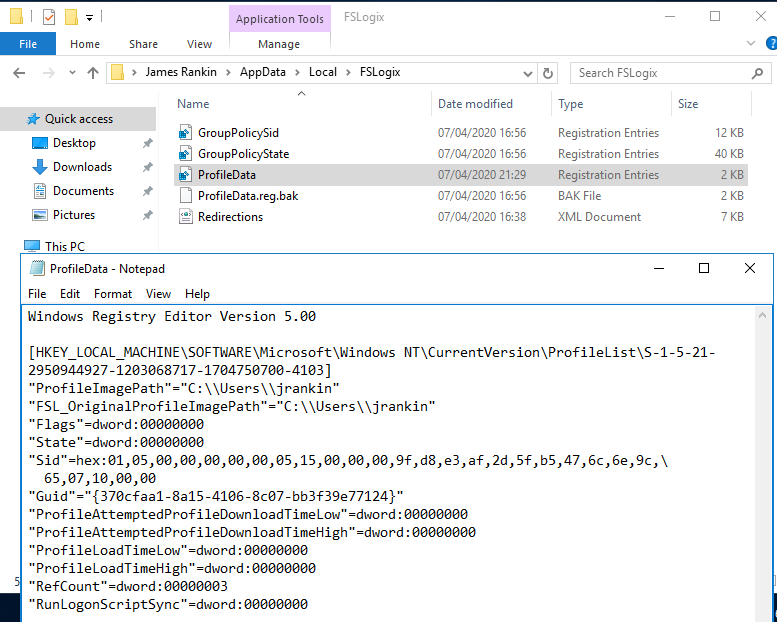
I think that FSLogix needs to be changed slightly to accomodate the behaviour of Group Policy caching, and possibly for this .reg fix to be extended to encompass it.
If you want to see a video demonstration of this issue, here it is:-
Big thanks due to Sargur Ravi Kiran from Microsoft who helped us greatly by pinpointing the issue.
![]()
Learned something new today. I’m done for the day lol. Nice find man.
Hmm, I was hopeful, but I don’t have the specific exclusion in place, but I do have the problems mentioned. Will enabling “Group Policy caching for servers” solve this problem?
If you don’t have caching enabled you shouldn’t see this issue. I would suggest a) remove all instances from HKLM of the USERSID mentioned, b) log the user on, c) run a gpupdate from the user session, d) ensure that the APPDATA\Local\GroupPolicy folder is created in the user profile, e) ensure that the Registry key mentioned is populated under DataStore, f) log back out and back in, see if all policies apply
Thanks for your time, James!
What I’ve done so far:
– A startup script that removes all instances from HKLM of the USERSID
– Disabled “Enable Group Policy Caching for Servers”
– gpupdate.exe
However, the GPOs are not applied at logon. Also, the folder you mention, “APPDATA\Local\GroupPolicy” is not created.
What works:
– executing gpupdate.exe after logon
– disabling “Block Inheritance”
I’m at a loss…
Regards,
Dennis.
Let’s be clear, if you have GPO Caching disabled those local folders will NEVER be created. What are you seeing in the System and GPO Operations logs when your GPOs fail to apply? This is the key part. If you see CSEs failing with “Unable to find the path specified”, then you are seeing the caching issue. If it is something else…well we can take it from there.
And naturally, make sure the APPDATA\Local\GroupPolicy folder writes back to the user profile 🙂
Nice work as per, James 🙂
I also have this problem but I do not have the specific exclusion in place nor do I have the caching enabled.
My environment is RDS with two RDSH servers and it’s for testing right now. I do have blocked Inheritance for OU that has RDS controllers and RDSH servers, and Loopback is configured to “Replace”. This problem happens everytime when user logs in second time. So first login -> user policies OK; second login -> gpresult/r: “INFO: The User does not have RSoP data.”.
If you suggest to delete HKLM values, that means I would have to delete them from every server everytime new user logs in? So this it not really an option.
And if I do not change anything else but to downgrade FSLogix from 2.9.7237.48865 to 2.9.7117.27413.
Could you please help me, am I missing something? Thank you in advance.
Not sure it’s the same issue then. Is your problem just “RSOP not working”, or are GPOs failing too? You could easily set up a Startup Script to clear the HKLM values.
I got the problem no matter what software I used, it’s not particularly an FSLogix thing in this instance.
True about the HKLM values, didn’t think of that :). I’m not 100% sure was GPO’s failing or just “RSOP not working”, I have to test it again to be sure, if I recall correctly, GPO’s was failing.
I have Server 2019, have you tested these with what Server version?
Also could you give me some advice with FSLogix ODFC and Profile container GPO’s. How should I configure them? Because if I have understood correctly Server 2019 does save search index data to profile not to machine anymore. Someone said “Search roaming” and “Store search database in Office 365 container” should NOT be configured in FSLogix GPO.
Thanks again.
Also, I watched the video and saw that you do not have Inheritance blocked and I presume that Loopback is not configured also. Could you test that do user GPO’s still work if you configure those, because I heard that someone got it to work if they disabled those.
Loopback is configured in Replace mode, inheritance is blocked one level up from the device OU
Re. Search, I trust what James K has done here to be fully correct – https://jkindon.com/2020/03/15/windows-search-in-server-2019-and-multi-session-windows-10/
Thank you again.
Great! Thanks for the summary
I *should* impacted by this bug at my current client, but am not
No issues with user policies applying
We do have intermittent failures to apply updated FSLogix polices via computer GPOs though. Maybe related? It’s not all, just 10%. We’ve taken to sealing the master images with the correct settings to get around it. I opened a case with Microsoft but it went nowhere
Owen
So I tested this again.
I installed FSLogix FSLogix_Apps_2.9.7237.48865 to new RDSH Server 2019 and I also deleted my user profile from network share. I made new FSLogix GPO’s and didn’t configure “Roaming search” nor “Store search database in Office 365 container”. New RDSH server is under new OU but that OU is inside the OU that has Inheritance blocked and Loopback set to “Replace”.
Outlook search now works.
Gpresult/r:
1 login – OK
2 login – INFO: The User does not have RSoP data.
-> Modifying user GPO -> gpupdate
settings did apply but gpresult/r now shows:
The user is part of the following security groups
____________________________________________________
Error: An unexpected error occurred.
OK so are we looking at a different problem here? GPO settings apply but RSoP fails?
Yes, GPO’s does apply.
But second login and gpresult/r shows:
“INFO: The User does not have RSoP data.”.
And if I modify GPO -> gpupdate, GPO does apply and gpresult/r shows:
some correct details but always ends with:
The user is part of the following security groups
____________________________________________________
Error: An unexpected error occurred.
OK this is a totally different issue to what I was experiencing. I would suggest raising a premier case with Microsoft.
Other people have this problem also:
https://social.msdn.microsoft.com/Forums/en-US/14bed90e-67a2-4100-a282-6c7b57b68fc9/gpo-user-policy-not-applied-when-using-fslogix-profile-container-used?forum=FSLogix
Other people have this problem also:
https://social.msdn.microsoft.com/Forums/en-US/14bed90e-67a2-4100-a282-6c7b57b68fc9/gpo-user-policy-not-applied-when-using-fslogix-profile-container-used?forum=FSLogix
Am I right in thinking this might fix the issue you are describing?
Configure this registry key.
DWORD GroupPolicyState = 0 under
HKLM\SOFTWARE\FSLogix\Profiles\
what exactly does the 0 vs 1 do with GroupPolicyState? Does it enable/diasable caching?
Nobody is entirely sure, as far as I know. It seems to be an undocumented key from FSLogix but it appears to fix the issue with RSOP failing when FSLogix is being used.
This indeed fixed the issue with RSoP. Thanks
Great that seemed to do the trick. Thanks.
Question about where to find this community redirections.xml file to start off with. I can’t seem to find any good starting points online. Where is the one you are referencing located?
https://stealthpuppy.com/fslogix-profile-containers-redirections/
Hi James,
I hope you are doing well.
I’m taking a chance you can help. I have configured FSLogix Office 365 Containers in conjunction with Citrix UPM. Almost everything is working (after much tweaking and testing) and I have included Outlook and Teams into the solution to assist with limiting Profile Bloat in the UPM profile. Teams is writing the 326MB back to the .VHDX file and the profile is not growing anymore. I close the first session where I set up Teams and Outlook, and log off to see the 0 Bytes Teams folder in the UPM\Local\AppData\Microsoft path in the profile, all great so far. I log back in, data pulls from the .VHDX file no problem and the Teams data is populated into the local profile on the VDA. I launch Outlook and the pre-configured user settings are there, mail opens without the need to re-enter all the user details. But Teams seems to have an issue opening. As mentioned all the files appear to be in the local AppData location as required, Teams does start on the machine because it is running in the system tray and you can click on Get Logs/Settings/Open and Quit. If you click open, Teams launches, but minimised and it looks like a blank window when you hover over the Teams icon in the taskbar. I cannot open Teams, maximise or anything with it…. I have checked Windows Application logs in Event Viewer….can’t seem to find any errors there, I also checked the logs in the system tray for Teams and can’t find anything telling there either. Nothing jumps out at me in the frxtray logs either and I’m a bit stumped as to what the issue may be. It’s the last hurdle in completing the move of Teams and Outlook from UPM to FSLogix Office containers, and I’m really a bit stumped now. I can’t even find anything in discussion forums anywhere where most issues are of the ‘white screen variety’ rather than this little gem I’ve managed to generate. 🙂 Do you have any thoughts or ideas? Thank you in advance. Steve
Do you have the Teams and Outlook folders excluded from UPM? Not sure whether you need to or not, tbf, but it might help.
Im having the opposite problem where at the first logon the FSlogix User policies dont apply, for instance we have policies that hide the C and D drives and on the first logon when the profile is being setup if the user goes into the File Explorer they can see those drives, they get other errors as well, but that one is the one that is consistent. I have to have the user logoff and back on right after the first logon to have all of the user policies apply correctly. Just wondering if anyone has any ideas about that.
Hi James,
Thanks for the great article. I followed your steps, but my FileSysPath is always C:\Windows\System32\GroupPoliy\User and not %LOCALAPPDATA%\GroupPolicy\DataStore\0\SysVol\domainname\Policies. How can I change that?
Best regards,
Flo
I’ve never seen that happen, what is your domain functional level?
Thanks for your quick response. My domain functional level is Windows Server 2012 R2. Do you think that cause the issue?
Group Policy Caching started with 2012 R2 so that should work OK. Very odd.
In my setup (All servers Windows Server 2019 functional level Windows 2012 R2) the location is also C:\Windows\System32\GroupPolicy instead of %LOCALAPPDATA%\GroupPolicy\DataStore\0\SysVol\domainname\Policies
I was reading your article because i came arcoss the problem that user settings where applied once and did not get reapplied. Exampe: registry settings for Office fonts and printer deployments. I did not configure GPO caching then. So i started with implementing GPO caching removed alle lines from HKLM\Software\Microsoft\Windows\CurrentVersion\Group Policy\DataStore\
I implemented the
GroupPolicyState = 0 under
HKLM\SOFTWARE\FSLogix\Profiles\
Now logon is much faster and Group policy is applied again. Nice!
Okay i will die here…
Anyone can help me a bit?
I set up fslogix on few computers and when and some of them log a profile for a user and other use another profile for the user….
Why does it not load the same profile on all computers? The profile exists only on the shared folder… and they all have full access…as proff when the second profile was created it was in the same darn folder as the first one….
Here are some logs:
Log file created 2020-09-14 at 19:07:04
UTC+02:00
Origin: C:\Program Files\FSLogix\Apps\frxsvc.exe (Version 2.9.7349.30108)
Windows 10.0.18362 (Windows 10 Pro 64-bit)
Computer Name: PC-SUPP-05 User Name: SYSTEM
WinDir: C:\Windows
User Profile: C:\Windows\system32\config\systemprofile
Profile Version: 6
Installed system RAM: 8085 MB (load: 29 %)
FSLogix Service Version 2.9.7349.30108 Status: RUNNING
FSLogix Kernel Driver Version 2.9.7349.30108 Status: RUNNING
FSLogix Kernel Virtualization Driver Version 2.9.7349.30108 Status: RUNNING
—————————————————————
[19:07:04.939][tid:00000e7c.000011a4][INFO] ===== Begin Session: EndShell
[19:07:04.939][tid:00000e7c.000011a4][INFO] User: S-1-5-21-2245420216-3298954963-992476483-1012 (teodora.stan)
[19:07:04.939][tid:00000e7c.000011a4][INFO] Acquiring mutex for user logoff
[19:07:04.939][tid:00000e7c.000011a4][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\LogonSyncMutexTimeout. Using default: 60000
[19:07:04.939][tid:00000e7c.000011a4][INFO] Mutex acquired
[19:07:04.970][tid:00000e7c.000011a4][INFO] Session configuration read (REG_SZ): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1012\ActivityId = ‘5afe0213-8aaa-0002-f359-fe5aaa8ad601’
[19:07:04.970][tid:00000e7c.000011a4][INFO] Outlook cached mode policy rule removed
[19:07:04.970][tid:00000e7c.000011a4][INFO] Session configuration read (DWORD): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1012\EnableSpecialRoamingProfile = ‘0’
[19:07:04.970][tid:00000e7c.000011a4][INFO] ===== End Session: EndShell
[19:07:05.080][tid:00000e7c.000011a4][INFO] ===== Begin Session: Logoff
[19:07:05.080][tid:00000e7c.000011a4][INFO] User: S-1-5-21-2245420216-3298954963-992476483-1012 (teodora.stan)
[19:07:05.080][tid:00000e7c.000011a4][INFO] Acquiring Lock for user logoff
[19:07:05.080][tid:00000e7c.000011a4][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\LogonSyncMutexTimeout. Using default: 60000
[19:07:05.080][tid:00000e7c.000011a4][INFO] Mutex acquired
[19:07:05.080][tid:00000e7c.000011a4][INFO] ===== Begin Session: Unload profile: teodora.stan
[19:07:05.080][tid:00000e7c.000011a4][INFO] User: teodora.stan. SID: S-1-5-21-2245420216-3298954963-992476483-1012.
[19:07:05.080][tid:00000e7c.000011a4][INFO] Session configuration read (REG_SZ): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1012\ActivityId = ‘5afe0213-8aaa-0002-f359-fe5aaa8ad601’
[19:07:05.080][tid:00000e7c.000011a4][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ConcurrentUserSessions. Using default: 1
[19:07:05.080][tid:00000e7c.000011a4][INFO] Profile refcount decremented to: 0
[19:07:05.080][tid:00000e7c.000011a4][INFO] Session configuration read (DWORD): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1012\AccessNetworkAsComputerObject = ‘0’
[19:07:05.080][tid:00000e7c.000011a4][INFO] Session configuration read (REG_SZ): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1012\ActivityId = ‘5afe0213-8aaa-0002-f359-fe5aaa8ad601’
[19:07:05.080][tid:00000e7c.000011a4][INFO] Session configuration read (REG_SZ): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1012\AttachVHDSDDL = ‘D:AI(A;;GA;;;SY)(A;;GA;;;BA)(A;;GA;;;BU)(A;;GA;;;WD)(A;;GA;;;RC)(A;;GA;;;AC)S:(ML;;NW;;;LW)’
[19:07:05.080][tid:00000e7c.000011a4][INFO] Session configuration read (DWORD): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1012\DisableRegistryLocalRedirect = ‘1’
[19:07:05.080][tid:00000e7c.000011a4][INFO] Session configuration read (DWORD): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1012\EnableSpecialRoamingProfile = ‘0’
[19:07:05.080][tid:00000e7c.000011a4][INFO] Session configuration read (DWORD): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1012\LockedRetryCount = ’12’
[19:07:05.080][tid:00000e7c.000011a4][INFO] Session configuration read (DWORD): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1012\LockedRetryInterval = ‘5’
[19:07:05.080][tid:00000e7c.000011a4][INFO] Session configuration read (DWORD): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1012\NoProfileContainingFolder = ‘0’
[19:07:05.080][tid:00000e7c.000011a4][INFO] Session configuration read (REG_SZ): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1012\ProfileDirSDDL = ”
[19:07:05.080][tid:00000e7c.000011a4][INFO] Session configuration read (DWORD): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1012\ProfileType = ‘0’
[19:07:05.080][tid:00000e7c.000011a4][INFO] Session configuration read (REG_SZ): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1012\RedirXMLSourceFolder = ”
[19:07:05.080][tid:00000e7c.000011a4][INFO] Session configuration read (REG_SZ): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1012\VHDRootFilePath = ‘\\10.10.0.149\FSLogixContainers\CSTeam\S-1-5-21-2245420216-3298954963-992476483-1012_teodora.stan\Profile_teodora.stan.vhd’
[19:07:05.080][tid:00000e7c.000011a4][INFO] Session configuration read (REG_SZ): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1012\VHDRODiffDiskFilePath = ‘C:\Windows\TEMP\S-1-5-21-2245420216-3298954963-992476483-1012_RO.vhd’
[19:07:05.080][tid:00000e7c.000011a4][INFO] Session configuration read (REG_SZ): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1012\VHDRWDiffDiskFilePath = ‘\\10.10.0.149\FSLogixContainers\CSTeam\S-1-5-21-2245420216-3298954963-992476483-1012_teodora.stan\RW.vhd’
[19:07:05.080][tid:00000e7c.000011a4][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\RemoveOrphanedOSTFilesOnLogoff. Using default: 0
[19:07:05.080][tid:00000e7c.000011a4][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\OutlookFolderPath. Using default: %userprofile%\AppData\Local\Microsoft\Outlook
[19:07:05.080][tid:00000e7c.000011a4][INFO] vhd(x) \\10.10.0.149\FSLogixContainers\CSTeam\S-1-5-21-2245420216-3298954963-992476483-1012_teodora.stan\Profile_teodora.stan.vhd has 39296.86 MB left (98.24 % free)
[19:07:05.080][tid:00000e7c.000011a4][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\RegisterAppNotifications. Using default: 1
[19:07:05.080][tid:00000e7c.000011a4][INFO] Prep3
[19:07:05.126][tid:00000e7c.000011a4][INFO] Accessing network as user object
[19:07:05.126][tid:00000e7c.000011a4][INFO] Removing Profile Redirections
[19:07:05.126][tid:00000e7c.000011a4][INFO] Removed redirection from C:\Users\teodora.stan\AppData\Roaming\Microsoft\Protect
[19:07:05.126][tid:00000e7c.000011a4][INFO] Removed redirection from C:\Users\teodora.stan\AppData\Roaming\Microsoft\Credentials
[19:07:05.126][tid:00000e7c.000011a4][INFO] Removed redirection from C:\Users\teodora.stan\AppData\Local\Microsoft\Credentials
[19:07:05.126][tid:00000e7c.000011a4][INFO] Mirroring exclude folder: AppData\Roaming\Microsoft\Protect\
[19:07:05.158][tid:00000e7c.000011a4][INFO] Mirroring exclude folder: AppData\Roaming\Microsoft\Credentials\
[19:07:05.189][tid:00000e7c.000011a4][INFO] Mirroring exclude folder: AppData\Local\Microsoft\Credentials\
[19:07:05.220][tid:00000e7c.000011a4][INFO] Removal of folder redirection complete
[19:07:05.251][tid:00000e7c.000011a4][INFO] Export profile registry info complete
[19:07:05.251][tid:00000e7c.000011a4][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\GroupPolicyState. Using default: 1
[19:07:05.251][tid:00000e7c.000011a4][INFO] Exported group policy sid key
[19:07:05.267][tid:00000e7c.000011a4][INFO] Exported group policy state key
[19:07:05.267][tid:00000e7c.000011a4][INFO] Removed redirection from C:\Users\teodora.stan
[19:07:05.267][tid:00000e7c.000011a4][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ControlTileService. Using default: 0
[19:07:05.267][tid:00000e7c.000011a4][INFO] Could not detach the VHD as the user ERROR: 1314. This is sometimes expected, trying again as SYSTEM
[19:07:05.579][tid:00000e7c.000011a4][INFO] Detached vhd(x)
[19:07:05.579][tid:00000e7c.000011a4][INFO] Detach request returning after 312 milliseconds
[19:07:05.579][tid:00000e7c.000011a4][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\KeepLocalDir. Using default: 0
[19:07:05.579][tid:00000e7c.000011a4][INFO] Directory removal queued: C:\Users\local_teodora.stan
[19:07:05.579][tid:00000e7c.000011a4][INFO] Device cleanup queued
[19:07:05.579][tid:00000e7c.000011a4][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\DeleteProfileOnLogoff. Using default: 1
[19:07:05.579][tid:00000e7c.000006f8][INFO] ===== Begin Session: Remove Local Directory
[19:07:05.579][tid:00000e7c.000006f8][INFO] Successfully removed C:\Users\local_teodora.stan
[19:07:05.579][tid:00000e7c.000006f8][INFO] ===== End Session: Remove Local Directory
[19:07:05.595][tid:00000e7c.00000e80][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ReAttachRetryCount. Using default: 60
[19:07:05.595][tid:00000e7c.00000e80][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ReAttachIntervalSeconds. Using default: 10
[19:07:05.595][tid:00000e7c.00000e80][INFO] ===== Begin Session: Volume re-attach
[19:07:05.595][tid:00000e7c.00000e80][INFO] ===== End Session: Volume re-attach
[19:07:05.689][tid:00000e7c.00002024][INFO] ===== Begin Session: Remove Unused Device Information
[19:07:05.720][tid:00000e7c.00002024][INFO] Devices removed: 4. Errors: 0
[19:07:05.720][tid:00000e7c.00002024][INFO] ===== End Session: Remove Unused Device Information
[19:07:07.142][tid:00000e7c.000011a4][INFO] Profile removed for sid S-1-5-21-2245420216-3298954963-992476483-1012
[19:07:07.142][tid:00000e7c.000011a4][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ShutdownOnUserLogoff. Using default: 0
[19:07:07.142][tid:00000e7c.000011a4][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\RebootOnUserLogoff. Using default: 0
[19:07:07.142][tid:00000e7c.000011a4][INFO] UnloadProfile successful. User: teodora.stan. SID: S-1-5-21-2245420216-3298954963-992476483-1012.
[19:07:07.142][tid:00000e7c.000011a4][INFO] unloadProfile time: 2063 milliseconds
[19:07:07.142][tid:00000e7c.000011a4][INFO] ===== End Session: Unload profile: teodora.stan
[19:07:07.142][tid:00000e7c.000011a4][INFO] ===== End Session: Logoff
[19:09:33.090][tid:00000e7c.00001f74][INFO] ===== Begin Session: Logon
[19:09:33.090][tid:00000e7c.00001f74][INFO] User: S-1-5-21-2245420216-3298954963-992476483-1012 (teodora.stan)
[19:09:33.090][tid:00000e7c.00001f74][INFO] Acquiring mutex for user logon
[19:09:33.090][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\LogonSyncMutexTimeout. Using default: 60000
[19:09:33.090][tid:00000e7c.00001f74][INFO] Mutex acquired
[19:09:33.090][tid:00000e7c.00001f74][INFO] ===== Begin Session: LoadProfile: teodora.stan
[19:09:33.090][tid:00000e7c.00001f74][INFO] Configuration Read (DWORD): SOFTWARE\FSLogix\Profiles\Enabled. Data: 1
[19:09:33.090][tid:00000e7c.00001f74][INFO] User: teodora.stan. SID: S-1-5-21-2245420216-3298954963-992476483-1012.
[19:09:33.090][tid:00000e7c.00001f74][INFO] Include group SID: S-1-5-21-2245420216-3298954963-992476483-1004
[19:09:33.090][tid:00000e7c.00001f74][INFO] Exclude group SID: S-1-5-21-2245420216-3298954963-992476483-1005
[19:09:33.090][tid:00000e7c.00001f74][INFO] User is a member of the include group
[19:09:33.090][tid:00000e7c.00001f74][INFO] Status set to 200: Setup in progress
[19:09:33.090][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\RedirectType. Using default: 2
[19:09:33.090][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ConcurrentUserSessions. Using default: 1
[19:09:33.090][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\VolumeWaitTimeMS. Using default: 20000
[19:09:33.090][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\DeleteLocalProfileWhenVHDShouldApply. Using default: 0
[19:09:33.090][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\FSLogixShellPath. Using default:
[19:09:33.090][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\AccessNetworkAsComputerObject. Using default: 0
[19:09:33.090][tid:00000e7c.00001f74][INFO] Accessing network as user object
[19:09:33.090][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\AttachVHDSDDL. Using default:
[19:09:33.090][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ProfileType. Using default: 0
[19:09:33.090][tid:00000e7c.00001f74][INFO] Profile type: Normal
[19:09:33.090][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\CCDLocations. Using default:
[19:09:33.090][tid:00000e7c.00001f74][INFO] Configuration Read (REG_SZ): SOFTWARE\FSLogix\Profiles\VHDLocations.
[19:09:33.090][tid:00000e7c.00001f74][INFO] VHDLocations found – configured to use Local Disk
[19:09:33.090][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\DiffDiskParentFolderPath. Using default: C:\Windows\TEMP\
[19:09:33.090][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\NoProfileContainingFolder. Using default: 0
[19:09:33.090][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\FlipFlopProfileDirectoryName. Using default: 0
[19:09:33.090][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\SIDDirNameMatch. Using default: %sid%_%username%
[19:09:33.090][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\VHDNameMatch. Using default: Profile*
[19:09:33.090][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\VolumeType. Using default: vhd
[19:09:33.122][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\LockedRetryCount. Using default: 12
[19:09:33.122][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\LockedRetryInterval. Using default: 5
[19:09:33.215][tid:00000e7c.00001f74][INFO] Attached vhd(x) successfully
[19:09:33.215][tid:00000e7c.00001f74][INFO] VHD attach request returning after 78 milliseconds
[19:09:33.215][tid:00000e7c.00000e80][INFO] Volume attach event
[19:09:33.262][tid:00000e7c.00001f74][INFO] Could not detach the VHD as the user ERROR: 1314. This is sometimes expected, trying again as SYSTEM
[19:09:33.293][tid:00000e7c.00001f74][INFO] Detached vhd(x)
[19:09:33.293][tid:00000e7c.00001f74][INFO] Detach request returning after 31 milliseconds
[19:09:33.293][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\DisableRegistryLocalRedirect. Using default: 1
[19:09:33.293][tid:00000e7c.00001f74][INFO] Profile VHD Path: \\10.10.0.149\FSLogixContainers\CSTeam\S-1-5-21-2245420216-3298954963-992476483-1012_teodora.stan\Profile_teodora.stan.vhd
[19:09:33.293][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\SIDDirNamePattern. Using default: %sid%_%username%
[19:09:33.309][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\VHDNamePattern. Using default: Profile_%username%
[19:09:33.309][tid:00000e7c.00001f74][INFO] User Profile Path: C:\Users\teodora.stan.FSL0
[19:09:33.325][tid:00000e7c.00000e80][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ReAttachRetryCount. Using default: 60
[19:09:33.325][tid:00000e7c.00000e80][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ReAttachIntervalSeconds. Using default: 10
[19:09:33.325][tid:00000e7c.00000e80][INFO] ===== Begin Session: Volume re-attach
[19:09:33.325][tid:00000e7c.00000e80][INFO] ===== End Session: Volume re-attach
[19:09:33.340][tid:00000e7c.00001f74][INFO] Attached vhd(x) successfully
[19:09:33.340][tid:00000e7c.00001f74][INFO] VHD attach request returning after 31 milliseconds
[19:09:33.340][tid:00000e7c.00001f74][INFO] VHD attached
[19:09:33.340][tid:00000e7c.00000e80][INFO] Volume attach event
[19:09:33.387][tid:00000e7c.00001f74][INFO] Volume name: \\?\Volume{67116ffa-187c-4345-acb2-cb21314f7bcc}\
[19:09:33.387][tid:00000e7c.00001f74][INFO] Profile format version 2
[19:09:33.387][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ProfileDirSDDL. Using default:
[19:09:33.387][tid:00000e7c.00001f74][INFO] Create user directory success
[19:09:33.387][tid:00000e7c.00001f74][INFO] Security looks good
[19:09:33.387][tid:00000e7c.00001f74][INFO] Added redirection C:\Users\teodora.stan.FSL0 -> \\?\Volume{67116ffa-187c-4345-acb2-cb21314f7bcc}\Profile
[19:09:33.387][tid:00000e7c.00001f74][INFO] Create mount point success
[19:09:33.403][tid:00000e7c.00001f74][INFO] Reg import process creation completed in 16 milliseconds
[19:09:33.434][tid:00000e7c.00001f74][INFO] Reg import execution completed in 31 milliseconds
[19:09:33.434][tid:00000e7c.00001f74][INFO] Import Profile Registry success
[19:09:33.434][tid:00000e7c.00001f74][INFO] Checking to see if cleanup necessary
[19:09:33.434][tid:00000e7c.00001f74][INFO] Removing junction: C:\Users\teodora.stan.FSL0. Adding junction C:\Users\teodora.stan.
[19:09:33.434][tid:00000e7c.00001f74][INFO] Removed redirection from C:\Users\teodora.stan.FSL0
[19:09:33.434][tid:00000e7c.00001f74][INFO] Added redirection C:\Users\teodora.stan -> \\?\Volume{67116ffa-187c-4345-acb2-cb21314f7bcc}\Profile
[19:09:33.434][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\KeepLocalDir. Using default: 0
[19:09:33.434][tid:00000e7c.00001f74][INFO] Local temp directory: C:\Users\local_teodora.stan
[19:09:33.434][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\RedirXMLSourceFolder. Using default:
[19:09:33.434][tid:00000e7c.00001f74][INFO] Reading profile folder redirections
[19:09:33.434][tid:00000e7c.00001f74][INFO] Adding redirections for Credential Manager
[19:09:33.434][tid:00000e7c.00001f74][INFO] Creating base folders for profile folder redirections
[19:09:33.434][tid:00000e7c.00001f74][INFO] Creating base folder ‘AppData\Roaming\Microsoft\Protect\’
[19:09:33.481][tid:00000e7c.00001f74][INFO] Mirror success: C:\Users\teodora.stan\AppData\Roaming\Microsoft\Protect -> C:\Users\local_teodora.stan\AppData\Roaming\Microsoft\Protect
[19:09:33.481][tid:00000e7c.00001f74][INFO] Creating base folder ‘AppData\Roaming\Microsoft\Credentials\’
[19:09:33.512][tid:00000e7c.00001f74][INFO] Mirror success: C:\Users\teodora.stan\AppData\Roaming\Microsoft\Credentials -> C:\Users\local_teodora.stan\AppData\Roaming\Microsoft\Credentials
[19:09:33.512][tid:00000e7c.00001f74][INFO] Creating base folder ‘AppData\Local\Microsoft\Credentials\’
[19:09:33.543][tid:00000e7c.00001f74][INFO] Mirror success: C:\Users\teodora.stan\AppData\Local\Microsoft\Credentials -> C:\Users\local_teodora.stan\AppData\Local\Microsoft\Credentials
[19:09:33.543][tid:00000e7c.00001f74][INFO] Adding exclude rule for folder ‘AppData\Roaming\Microsoft\Protect\’
[19:09:33.543][tid:00000e7c.00001f74][INFO] Added redirection C:\Users\teodora.stan\AppData\Roaming\Microsoft\Protect -> C:\Users\local_teodora.stan\AppData\Roaming\Microsoft\Protect
[19:09:33.543][tid:00000e7c.00001f74][INFO] Adding exclude rule for folder ‘AppData\Roaming\Microsoft\Credentials\’
[19:09:33.543][tid:00000e7c.00001f74][INFO] Added redirection C:\Users\teodora.stan\AppData\Roaming\Microsoft\Credentials -> C:\Users\local_teodora.stan\AppData\Roaming\Microsoft\Credentials
[19:09:33.543][tid:00000e7c.00001f74][INFO] Adding exclude rule for folder ‘AppData\Local\Microsoft\Credentials\’
[19:09:33.543][tid:00000e7c.00001f74][INFO] Added redirection C:\Users\teodora.stan\AppData\Local\Microsoft\Credentials -> C:\Users\local_teodora.stan\AppData\Local\Microsoft\Credentials
[19:09:33.543][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\GroupPolicyState. Using default: 1
[19:09:33.559][tid:00000e7c.00001f74][INFO] Imported group policy sid key
[19:09:33.559][tid:00000e7c.00001f74][INFO] Imported group policy state key
[19:09:33.559][tid:00000e7c.00001f74][INFO] Folder redirections created
[19:09:33.559][tid:00000e7c.00001f74][INFO] Status set to 0: Success
[19:09:33.559][tid:00000e7c.00001f74][INFO] Profile refcount incremented to: 1
[19:09:33.559][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\CleanOutNotifications. Using default: 1
[19:09:33.559][tid:00000e7c.00001f74][INFO] Prep1
[19:09:33.559][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\RegisterAppNotifications. Using default: 1
[19:09:33.559][tid:00000e7c.00001f74][INFO] Prep2
[19:09:33.637][tid:00000e7c.00001f74][INFO] OneDriveTemp setup
[19:09:33.637][tid:00000e7c.00001f74][INFO] C:\OneDriveTemp\S-1-5-21-2245420216-3298954963-992476483-1012 –> \\?\Volume{67116ffa-187c-4345-acb2-cb21314f7bcc}\ODTemp
[19:09:33.637][tid:00000e7c.00001f74][INFO] OneDriveTemp setup successful
[19:09:33.637][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\PreventLoginWithFailure. Using default: 0
[19:09:33.637][tid:00000e7c.00001f74][INFO] LoadProfile successful. User: teodora.stan. SID: S-1-5-21-2245420216-3298954963-992476483-1012.
[19:09:33.637][tid:00000e7c.00001f74][INFO] loadProfile time: 547 milliseconds
[19:09:33.637][tid:00000e7c.00001f74][INFO] ===== End Session: LoadProfile: teodora.stan
[19:09:33.637][tid:00000e7c.00001f74][INFO] ===== End Session: Logon
[19:09:33.762][tid:00000e7c.00001f74][INFO] ===== Begin Session: StartShell
[19:09:33.762][tid:00000e7c.00001f74][INFO] User: S-1-5-21-2245420216-3298954963-992476483-1012 (teodora.stan)
[19:09:33.762][tid:00000e7c.00001f74][INFO] Acquiring mutex for user logon
[19:09:33.762][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\LogonSyncMutexTimeout. Using default: 60000
[19:09:33.762][tid:00000e7c.00001f74][INFO] Mutex acquired
[19:09:33.793][tid:00000e7c.00001f74][INFO] ===== Begin Session: Logon notification: teodora.stan
[19:09:33.793][tid:00000e7c.00001f74][INFO] Session configuration read (REG_SZ): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1012\ActivityId = ‘5afe0213-8aaa-0003-13d1-fe5aaa8ad601’
[19:09:33.793][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ConcurrentUserSessions. Using default: 1
[19:09:33.793][tid:00000e7c.00001f74][INFO] Checking Profile Data Export for S-1-5-21-2245420216-3298954963-992476483-1012
[19:09:33.809][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\SetTempToLocalPath. Using default: 3
[19:09:33.809][tid:00000e7c.00001f74][INFO] Initiating set up of TMP and TEMP environment variables to local disk
[19:09:33.809][tid:00000e7c.00001f74][INFO] Creating temp directory: C:\Users\local_teodora.stan\Temp
[19:09:33.809][tid:00000e7c.00001f74][INFO] Setting TMP and TEMP registry entries to: C:\Users\local_teodora.stan\Temp
[19:09:33.809][tid:00000e7c.00001f74][INFO] Setting INetCache folder
[19:09:33.809][tid:00000e7c.00001f74][INFO] INetCache folder successfully changed
[19:09:33.903][tid:00000e7c.00001f74][INFO] Profile data exported successfully
[19:09:33.903][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\OutlookCachedMode. Using default: 1
[19:09:33.903][tid:00000e7c.00001f74][INFO] Outlook cached mode policy rule added
[19:09:33.903][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Apps\RoamSearch. Using default: 0
[19:09:33.903][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\Policies\FSLogix\ODFC\RoamSearch. Using default: 0
[19:09:33.903][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\RoamSearch. Using default: 0
[19:09:33.903][tid:00000e7c.00001f74][INFO] Search is not configured
[19:09:33.903][tid:00000e7c.00001f74][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\EnableSpecialRoamingProfile. Using default: 0
[19:09:33.918][tid:00000e7c.00001f74][INFO] ===== End Session: Logon notification: teodora.stan
[19:09:33.918][tid:00000e7c.00001f74][INFO] ===== End Session: StartShell
And second one:
Log file created 2020-09-14 at 19:21:27
UTC+02:00
Origin: C:\Program Files\FSLogix\Apps\frxsvc.exe (Version 2.9.7349.30108)
Windows 10.0.18362 (Windows 10 Pro 64-bit)
Computer Name: PC-SUPP-04 User Name: SYSTEM
WinDir: C:\Windows
User Profile: C:\Windows\system32\config\systemprofile
Profile Version: 6
Installed system RAM: 8085 MB (load: 29 %)
FSLogix Service Version 2.9.7349.30108 Status: RUNNING
FSLogix Kernel Driver Version 2.9.7349.30108 Status: RUNNING
FSLogix Kernel Virtualization Driver Version 2.9.7349.30108 Status: RUNNING
—————————————————————
[19:21:27.768][tid:00000f04.00002350][INFO] ===== Begin Session: EndShell
[19:21:27.768][tid:00000f04.00002350][INFO] User: S-1-5-21-2245420216-3298954963-992476483-1011 (teodora.stan)
[19:21:27.768][tid:00000f04.00002350][INFO] Acquiring mutex for user logoff
[19:21:27.768][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\LogonSyncMutexTimeout. Using default: 60000
[19:21:27.768][tid:00000f04.00002350][INFO] Mutex acquired
[19:21:27.784][tid:00000f04.00002350][INFO] Session configuration read (REG_SZ): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1011\ActivityId = ‘0fcf772d-877b-0003-a8a1-da0f7b87d601’
[19:21:27.784][tid:00000f04.00002350][INFO] Outlook cached mode policy rule removed
[19:21:27.799][tid:00000f04.00002350][INFO] ===== End Session: EndShell
[19:21:27.908][tid:00000f04.00002350][INFO] ===== Begin Session: Logoff
[19:21:27.908][tid:00000f04.00002350][INFO] User: S-1-5-21-2245420216-3298954963-992476483-1011 (teodora.stan)
[19:21:27.908][tid:00000f04.00002350][INFO] Acquiring Lock for user logoff
[19:21:27.908][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\LogonSyncMutexTimeout. Using default: 60000
[19:21:27.908][tid:00000f04.00002350][INFO] Mutex acquired
[19:21:27.908][tid:00000f04.00002350][INFO] ===== Begin Session: Unload profile: teodora.stan
[19:21:27.908][tid:00000f04.00002350][INFO] User: teodora.stan. SID: S-1-5-21-2245420216-3298954963-992476483-1011.
[19:21:27.908][tid:00000f04.00002350][INFO] Session configuration read (REG_SZ): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1011\ActivityId = ‘0fcf772d-877b-0003-a8a1-da0f7b87d601’
[19:21:27.908][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ConcurrentUserSessions. Using default: 1
[19:21:27.908][tid:00000f04.00002350][INFO] Profile refcount decremented to: 0
[19:21:27.908][tid:00000f04.00002350][INFO] Session configuration read (DWORD): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1011\AccessNetworkAsComputerObject = ‘0’
[19:21:27.908][tid:00000f04.00002350][INFO] Session configuration read (REG_SZ): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1011\ActivityId = ‘0fcf772d-877b-0003-a8a1-da0f7b87d601’
[19:21:27.908][tid:00000f04.00002350][INFO] Session configuration read (REG_SZ): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1011\AttachVHDSDDL = ‘D:AI(A;;GA;;;SY)(A;;GA;;;BA)(A;;GA;;;BU)(A;;GA;;;WD)(A;;GA;;;RC)(A;;GA;;;AC)S:(ML;;NW;;;LW)’
[19:21:27.908][tid:00000f04.00002350][INFO] Session configuration read (DWORD): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1011\DisableRegistryLocalRedirect = ‘1’
[19:21:27.908][tid:00000f04.00002350][INFO] Session configuration read (DWORD): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1011\LockedRetryCount = ’12’
[19:21:27.908][tid:00000f04.00002350][INFO] Session configuration read (DWORD): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1011\LockedRetryInterval = ‘5’
[19:21:27.908][tid:00000f04.00002350][INFO] Session configuration read (DWORD): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1011\NoProfileContainingFolder = ‘0’
[19:21:27.908][tid:00000f04.00002350][INFO] Session configuration read (DWORD): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1011\ProfileType = ‘0’
[19:21:27.908][tid:00000f04.00002350][INFO] Session configuration read (REG_SZ): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1011\SIDDirSDDL = ”
[19:21:27.908][tid:00000f04.00002350][INFO] Session configuration read (REG_SZ): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1011\VHDRootFilePath = ‘\\10.10.0.149\FSLogixContainers\CSTeam\S-1-5-21-2245420216-3298954963-992476483-1011_teodora.stan\Profile_teodora.stan.vhd’
[19:21:27.908][tid:00000f04.00002350][INFO] Session configuration read (REG_SZ): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1011\VHDRODiffDiskFilePath = ‘C:\Windows\TEMP\S-1-5-21-2245420216-3298954963-992476483-1011_RO.vhd’
[19:21:27.908][tid:00000f04.00002350][INFO] Session configuration read (REG_SZ): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1011\VHDRWDiffDiskFilePath = ‘\\10.10.0.149\FSLogixContainers\CSTeam\S-1-5-21-2245420216-3298954963-992476483-1011_teodora.stan\RW.vhd’
[19:21:27.908][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\RemoveOrphanedOSTFilesOnLogoff. Using default: 0
[19:21:27.908][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\OutlookFolderPath. Using default: %userprofile%\AppData\Local\Microsoft\Outlook
[19:21:27.908][tid:00000f04.00002350][INFO] vhd(x) \\10.10.0.149\FSLogixContainers\CSTeam\S-1-5-21-2245420216-3298954963-992476483-1011_teodora.stan\Profile_teodora.stan.vhd has 39526.32 MB left (98.82 % free)
[19:21:27.908][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\RegisterAppNotifications. Using default: 1
[19:21:27.908][tid:00000f04.00002350][INFO] Prep3
[19:21:27.955][tid:00000f04.00002350][INFO] Accessing network as user object
[19:21:27.955][tid:00000f04.00002350][INFO] Adjusting symlinks
[19:21:28.158][tid:00000f04.00002350][INFO] Removing Profile Redirections
[19:21:28.158][tid:00000f04.00002350][INFO] Removed redirection from C:\Users\teodora.stan\AppData\Roaming\Microsoft\Protect
[19:21:28.158][tid:00000f04.00002350][INFO] Removed redirection from C:\Users\teodora.stan\AppData\Roaming\Microsoft\Credentials
[19:21:28.158][tid:00000f04.00002350][INFO] Removed redirection from C:\Users\teodora.stan\AppData\Local\Microsoft\Credentials
[19:21:28.158][tid:00000f04.00002350][INFO] Mirroring exclude folder: AppData\Roaming\Microsoft\Protect\
[19:21:28.221][tid:00000f04.00002350][INFO] Mirroring exclude folder: AppData\Roaming\Microsoft\Credentials\
[19:21:28.252][tid:00000f04.00002350][INFO] Mirroring exclude folder: AppData\Local\Microsoft\Credentials\
[19:21:28.283][tid:00000f04.00002350][INFO] Removal of folder redirection complete
[19:21:28.315][tid:00000f04.00002350][INFO] Export profile registry info complete
[19:21:28.315][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\GroupPolicyState. Using default: 1
[19:21:28.315][tid:00000f04.00002350][INFO] Exported group policy sid key
[19:21:28.330][tid:00000f04.00002350][INFO] Exported group policy state key
[19:21:28.330][tid:00000f04.00002350][INFO] Removed redirection from C:\Users\teodora.stan
[19:21:28.330][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ControlTileService. Using default: 0
[19:21:28.330][tid:00000f04.00002350][INFO] Could not detach the VHD as the user ERROR: 1314. This is sometimes expected, trying again as SYSTEM
[19:21:29.127][tid:00000f04.00002350][INFO] Detached vhd(x)
[19:21:29.127][tid:00000f04.00002350][INFO] Detach request returning after 797 milliseconds
[19:21:29.127][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\KeepLocalDir. Using default: 0
[19:21:29.127][tid:00000f04.00002350][INFO] Directory removal queued: C:\Users\local_teodora.stan
[19:21:29.127][tid:00000f04.00002350][INFO] Device cleanup queued
[19:21:29.127][tid:00000f04.00000718][INFO] ===== Begin Session: Remove Local Directory
[19:21:29.127][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\DeleteProfileOnLogoff. Using default: 1
[19:21:29.143][tid:00000f04.00000718][INFO] Successfully removed C:\Users\local_teodora.stan
[19:21:29.143][tid:00000f04.00000718][INFO] ===== End Session: Remove Local Directory
[19:21:29.143][tid:00000f04.00001b54][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ReAttachRetryCount. Using default: 60
[19:21:29.143][tid:00000f04.00001b54][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ReAttachIntervalSeconds. Using default: 10
[19:21:29.143][tid:00000f04.00001b54][INFO] ===== Begin Session: Volume re-attach
[19:21:29.143][tid:00000f04.00001b54][INFO] ===== End Session: Volume re-attach
[19:21:29.252][tid:00000f04.00002608][INFO] ===== Begin Session: Remove Unused Device Information
[19:21:29.283][tid:00000f04.00002608][INFO] Devices removed: 4. Errors: 0
[19:21:29.283][tid:00000f04.00002608][INFO] ===== End Session: Remove Unused Device Information
[19:21:31.001][tid:00000f04.00002350][INFO] Profile removed for sid S-1-5-21-2245420216-3298954963-992476483-1011
[19:21:31.001][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ShutdownOnUserLogoff. Using default: 0
[19:21:31.001][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\RebootOnUserLogoff. Using default: 0
[19:21:31.001][tid:00000f04.00002350][INFO] UnloadProfile successful. User: teodora.stan. SID: S-1-5-21-2245420216-3298954963-992476483-1011.
[19:21:31.001][tid:00000f04.00002350][INFO] unloadProfile time: 3094 milliseconds
[19:21:31.001][tid:00000f04.00002350][INFO] ===== End Session: Unload profile: teodora.stan
[19:21:31.001][tid:00000f04.00002350][INFO] ===== End Session: Logoff
[19:22:04.605][tid:00000f04.00002350][INFO] ===== Begin Session: Logon
[19:22:04.605][tid:00000f04.00002350][INFO] User: S-1-5-21-2245420216-3298954963-992476483-1011 (teodora.stan)
[19:22:04.605][tid:00000f04.00002350][INFO] Acquiring mutex for user logon
[19:22:04.605][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\LogonSyncMutexTimeout. Using default: 60000
[19:22:04.605][tid:00000f04.00002350][INFO] Mutex acquired
[19:22:04.605][tid:00000f04.00002350][INFO] ===== Begin Session: LoadProfile: teodora.stan
[19:22:04.605][tid:00000f04.00002350][INFO] Configuration Read (DWORD): SOFTWARE\FSLogix\Profiles\Enabled. Data: 1
[19:22:04.605][tid:00000f04.00002350][INFO] User: teodora.stan. SID: S-1-5-21-2245420216-3298954963-992476483-1011.
[19:22:04.605][tid:00000f04.00002350][INFO] Include group SID: S-1-5-21-2245420216-3298954963-992476483-1003
[19:22:04.605][tid:00000f04.00002350][INFO] Exclude group SID: S-1-5-21-2245420216-3298954963-992476483-1004
[19:22:04.605][tid:00000f04.00002350][INFO] User is a member of the include group
[19:22:04.605][tid:00000f04.00002350][INFO] Status set to 200: Setup in progress
[19:22:04.605][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\RedirectType. Using default: 2
[19:22:04.605][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ConcurrentUserSessions. Using default: 1
[19:22:04.605][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\VolumeWaitTimeMS. Using default: 20000
[19:22:04.605][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\DeleteLocalProfileWhenVHDShouldApply. Using default: 0
[19:22:04.605][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\FSLogixShellPath. Using default:
[19:22:04.605][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\AccessNetworkAsComputerObject. Using default: 0
[19:22:04.605][tid:00000f04.00002350][INFO] Accessing network as user object
[19:22:04.605][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\AttachVHDSDDL. Using default:
[19:22:04.605][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ProfileType. Using default: 0
[19:22:04.605][tid:00000f04.00002350][INFO] Profile type: Normal
[19:22:04.605][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\CCDLocations. Using default:
[19:22:04.605][tid:00000f04.00002350][INFO] Configuration Read (REG_SZ): SOFTWARE\FSLogix\Profiles\VHDLocations.
[19:22:04.605][tid:00000f04.00002350][INFO] VHDLocations found – configured to use Local Disk
[19:22:04.605][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\DiffDiskParentFolderPath. Using default: C:\Windows\TEMP\
[19:22:04.605][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\NoProfileContainingFolder. Using default: 0
[19:22:04.605][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\FlipFlopProfileDirectoryName. Using default: 0
[19:22:04.605][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\SIDDirNameMatch. Using default: %sid%_%username%
[19:22:04.605][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\VHDNameMatch. Using default: Profile*
[19:22:04.605][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\VolumeType. Using default: vhd
[19:22:04.636][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\LockedRetryCount. Using default: 12
[19:22:04.636][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\LockedRetryInterval. Using default: 5
[19:22:04.683][tid:00000f04.00002350][INFO] Attached vhd(x) successfully
[19:22:04.683][tid:00000f04.00002350][INFO] VHD attach request returning after 31 milliseconds
[19:22:04.683][tid:00000f04.00001b54][INFO] Volume attach event
[19:22:04.730][tid:00000f04.00002350][INFO] Could not detach the VHD as the user ERROR: 1314. This is sometimes expected, trying again as SYSTEM
[19:22:04.761][tid:00000f04.00002350][INFO] Detached vhd(x)
[19:22:04.761][tid:00000f04.00002350][INFO] Detach request returning after 31 milliseconds
[19:22:04.761][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\DisableRegistryLocalRedirect. Using default: 1
[19:22:04.761][tid:00000f04.00002350][INFO] Profile VHD Path: \\10.10.0.149\FSLogixContainers\CSTeam\S-1-5-21-2245420216-3298954963-992476483-1011_teodora.stan\Profile_teodora.stan.vhd
[19:22:04.761][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\SIDDirNamePattern. Using default: %sid%_%username%
[19:22:04.761][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\VHDNamePattern. Using default: Profile_%username%
[19:22:04.761][tid:00000f04.00002350][INFO] User Profile Path: C:\Users\teodora.stan.FSL0
[19:22:04.808][tid:00000f04.00002350][INFO] Attached vhd(x) successfully
[19:22:04.808][tid:00000f04.00002350][INFO] VHD attach request returning after 31 milliseconds
[19:22:04.808][tid:00000f04.00002350][INFO] VHD attached
[19:22:04.839][tid:00000f04.00001b54][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ReAttachRetryCount. Using default: 60
[19:22:04.839][tid:00000f04.00001b54][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ReAttachIntervalSeconds. Using default: 10
[19:22:04.839][tid:00000f04.00001b54][INFO] ===== Begin Session: Volume re-attach
[19:22:04.839][tid:00000f04.00001b54][INFO] ===== End Session: Volume re-attach
[19:22:04.839][tid:00000f04.00001b54][INFO] Volume attach event
[19:22:04.855][tid:00000f04.00002350][INFO] Volume name: \\?\Volume{abb41c3f-252e-4679-805b-393060aed0af}\
[19:22:04.855][tid:00000f04.00002350][INFO] Profile format version 2
[19:22:04.855][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ProfileDirSDDL. Using default:
[19:22:04.855][tid:00000f04.00002350][INFO] Create user directory success
[19:22:04.855][tid:00000f04.00002350][INFO] Security looks good
[19:22:04.855][tid:00000f04.00002350][INFO] Added redirection C:\Users\teodora.stan.FSL0 -> \\?\Volume{abb41c3f-252e-4679-805b-393060aed0af}\Profile
[19:22:04.855][tid:00000f04.00002350][INFO] Create mount point success
[19:22:04.870][tid:00000f04.00002350][INFO] Reg import process creation completed in 16 milliseconds
[19:22:04.902][tid:00000f04.00001278][INFO] ===== Begin Session: Profile Directory Changed: S-1-5-21-2245420216-3298954963-992476483-1011
[19:22:04.902][tid:00000f04.00001278][INFO] New Profile Directory: C:\Users\teodora.stan
[19:22:04.902][tid:00000f04.00001278][INFO] ===== End Session: Profile Directory Changed: S-1-5-21-2245420216-3298954963-992476483-1011
[19:22:04.902][tid:00000f04.00002350][INFO] Reg import execution completed in 31 milliseconds
[19:22:04.902][tid:00000f04.00002350][INFO] Import Profile Registry success
[19:22:04.902][tid:00000f04.00002350][INFO] Checking to see if cleanup necessary
[19:22:04.902][tid:00000f04.00002350][INFO] Removing junction: C:\Users\teodora.stan.FSL0. Adding junction C:\Users\teodora.stan.
[19:22:04.902][tid:00000f04.00002350][INFO] Removed redirection from C:\Users\teodora.stan.FSL0
[19:22:04.902][tid:00000f04.00002350][INFO] Added redirection C:\Users\teodora.stan -> \\?\Volume{abb41c3f-252e-4679-805b-393060aed0af}\Profile
[19:22:04.902][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\KeepLocalDir. Using default: 0
[19:22:04.902][tid:00000f04.00002350][INFO] Local temp directory: C:\Users\local_teodora.stan
[19:22:04.902][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\RedirXMLSourceFolder. Using default:
[19:22:04.902][tid:00000f04.00002350][INFO] Reading profile folder redirections
[19:22:04.902][tid:00000f04.00002350][INFO] Adding redirections for Credential Manager
[19:22:04.902][tid:00000f04.00002350][INFO] Creating base folders for profile folder redirections
[19:22:04.902][tid:00000f04.00002350][INFO] Creating base folder ‘AppData\Roaming\Microsoft\Protect\’
[19:22:04.948][tid:00000f04.00002350][INFO] Mirror success: C:\Users\teodora.stan\AppData\Roaming\Microsoft\Protect -> C:\Users\local_teodora.stan\AppData\Roaming\Microsoft\Protect
[19:22:04.948][tid:00000f04.00002350][INFO] Creating base folder ‘AppData\Roaming\Microsoft\Credentials\’
[19:22:04.995][tid:00000f04.00002350][INFO] Mirror success: C:\Users\teodora.stan\AppData\Roaming\Microsoft\Credentials -> C:\Users\local_teodora.stan\AppData\Roaming\Microsoft\Credentials
[19:22:04.995][tid:00000f04.00002350][INFO] Creating base folder ‘AppData\Local\Microsoft\Credentials\’
[19:22:05.027][tid:00000f04.00002350][INFO] Mirror success: C:\Users\teodora.stan\AppData\Local\Microsoft\Credentials -> C:\Users\local_teodora.stan\AppData\Local\Microsoft\Credentials
[19:22:05.027][tid:00000f04.00002350][INFO] Adding exclude rule for folder ‘AppData\Roaming\Microsoft\Protect\’
[19:22:05.027][tid:00000f04.00002350][INFO] Added redirection C:\Users\teodora.stan\AppData\Roaming\Microsoft\Protect -> C:\Users\local_teodora.stan\AppData\Roaming\Microsoft\Protect
[19:22:05.027][tid:00000f04.00002350][INFO] Adding exclude rule for folder ‘AppData\Roaming\Microsoft\Credentials\’
[19:22:05.027][tid:00000f04.00002350][INFO] Added redirection C:\Users\teodora.stan\AppData\Roaming\Microsoft\Credentials -> C:\Users\local_teodora.stan\AppData\Roaming\Microsoft\Credentials
[19:22:05.027][tid:00000f04.00002350][INFO] Adding exclude rule for folder ‘AppData\Local\Microsoft\Credentials\’
[19:22:05.027][tid:00000f04.00002350][INFO] Added redirection C:\Users\teodora.stan\AppData\Local\Microsoft\Credentials -> C:\Users\local_teodora.stan\AppData\Local\Microsoft\Credentials
[19:22:05.027][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\GroupPolicyState. Using default: 1
[19:22:05.027][tid:00000f04.00002350][INFO] Imported group policy sid key
[19:22:05.027][tid:00000f04.00002350][INFO] Imported group policy state key
[19:22:05.027][tid:00000f04.00002350][INFO] Folder redirections created
[19:22:05.027][tid:00000f04.00002350][INFO] Status set to 0: Success
[19:22:05.027][tid:00000f04.00002350][INFO] Profile refcount incremented to: 1
[19:22:05.027][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\CleanOutNotifications. Using default: 1
[19:22:05.027][tid:00000f04.00002350][INFO] Prep1
[19:22:05.027][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\RegisterAppNotifications. Using default: 1
[19:22:05.027][tid:00000f04.00002350][INFO] Prep2
[19:22:05.073][tid:00000f04.00002350][INFO] OneDriveTemp setup
[19:22:05.073][tid:00000f04.00002350][INFO] C:\OneDriveTemp\S-1-5-21-2245420216-3298954963-992476483-1011 –> \\?\Volume{abb41c3f-252e-4679-805b-393060aed0af}\ODTemp
[19:22:05.073][tid:00000f04.00002350][INFO] OneDriveTemp setup successful
[19:22:05.073][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\PreventLoginWithFailure. Using default: 0
[19:22:05.089][tid:00000f04.00002350][INFO] LoadProfile successful. User: teodora.stan. SID: S-1-5-21-2245420216-3298954963-992476483-1011.
[19:22:05.089][tid:00000f04.00002350][INFO] loadProfile time: 484 milliseconds
[19:22:05.089][tid:00000f04.00002350][INFO] ===== End Session: LoadProfile: teodora.stan
[19:22:05.089][tid:00000f04.00002350][INFO] ===== End Session: Logon
[19:22:05.230][tid:00000f04.00002350][INFO] ===== Begin Session: StartShell
[19:22:05.230][tid:00000f04.00002350][INFO] User: S-1-5-21-2245420216-3298954963-992476483-1011 (teodora.stan)
[19:22:05.230][tid:00000f04.00002350][INFO] Acquiring mutex for user logon
[19:22:05.230][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\LogonSyncMutexTimeout. Using default: 60000
[19:22:05.230][tid:00000f04.00002350][INFO] Mutex acquired
[19:22:05.230][tid:00000f04.00002350][INFO] ===== Begin Session: Logon notification: teodora.stan
[19:22:05.230][tid:00000f04.00002350][INFO] Session configuration read (REG_SZ): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-2245420216-3298954963-992476483-1011\ActivityId = ‘0fcf772d-877b-0003-08e2-da0f7b87d601’
[19:22:05.230][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ConcurrentUserSessions. Using default: 1
[19:22:05.230][tid:00000f04.00002350][INFO] Checking Profile Data Export for S-1-5-21-2245420216-3298954963-992476483-1011
[19:22:05.230][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\SetTempToLocalPath. Using default: 3
[19:22:05.230][tid:00000f04.00002350][INFO] Initiating set up of TMP and TEMP environment variables to local disk
[19:22:05.230][tid:00000f04.00002350][INFO] Creating temp directory: C:\Users\local_teodora.stan\Temp
[19:22:05.230][tid:00000f04.00002350][INFO] Setting TMP and TEMP registry entries to: C:\Users\local_teodora.stan\Temp
[19:22:05.230][tid:00000f04.00002350][INFO] Setting INetCache folder
[19:22:05.245][tid:00000f04.00002350][INFO] INetCache folder successfully changed
[19:22:05.370][tid:00000f04.00002350][INFO] Profile data exported successfully
[19:22:05.370][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\OutlookCachedMode. Using default: 1
[19:22:05.370][tid:00000f04.00002350][INFO] Outlook cached mode policy rule added
[19:22:05.370][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Apps\RoamSearch. Using default: 0
[19:22:05.370][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\Policies\FSLogix\ODFC\RoamSearch. Using default: 0
[19:22:05.370][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\RoamSearch. Using default: 0
[19:22:05.370][tid:00000f04.00002350][INFO] Search is not configured
[19:22:05.370][tid:00000f04.00002350][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\EnableSpecialRoamingProfile. Using default: 0
[19:22:05.386][tid:00000f04.00002350][INFO] ===== End Session: Logon notification: teodora.stan
[19:22:05.386][tid:00000f04.00002350][INFO] ===== End Session: StartShell
I dont get it… what im doing wrong…Anyone can help please?
Non-domain joined, possibly?
Hi James, I am getting issue where user VHDX files is getting locked. This is the log file and I cannot see any error. Is it I am missing something.
[07:02:58.322][tid:0000149c.0000257c][INFO] ===== Begin Session: Logon
[07:02:58.322][tid:0000149c.0000257c][INFO] User: S-1-5-21-966205532-1977663930-808559644-15368 (hartp)
[07:02:58.323][tid:0000149c.0000257c][INFO] Acquiring mutex for user logon
[07:02:58.323][tid:0000149c.0000257c][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\LogonSyncMutexTimeout. Using default: 60000
[07:02:58.323][tid:0000149c.0000257c][INFO] Mutex acquired
[07:02:58.323][tid:0000149c.0000257c][INFO] ===== Begin Session: LoadProfile: hartp
[07:02:58.323][tid:0000149c.0000257c][INFO] Configuration Read (DWORD): SOFTWARE\FSLogix\Profiles\Enabled. Data: 1
[07:02:58.323][tid:0000149c.0000257c][INFO] User: hartp. SID: S-1-5-21-966205532-1977663930-808559644-15368.
[07:02:58.324][tid:0000149c.0000257c][INFO] Include group SID: S-1-5-21-3322214072-4118122286-2229963527-1008
[07:02:58.324][tid:0000149c.0000257c][INFO] Exclude group SID: S-1-5-21-3322214072-4118122286-2229963527-1009
[07:02:58.324][tid:0000149c.0000257c][INFO] User is a member of the include group
[07:02:58.324][tid:0000149c.0000257c][INFO] Status set to 200: Setup in progress
[07:02:58.324][tid:0000149c.0000257c][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\RedirectType. Using default: 2
[07:02:58.324][tid:0000149c.0000257c][INFO] Configuration Read (DWORD): SOFTWARE\FSLogix\Profiles\ConcurrentUserSessions. Data: 1
[07:02:58.326][tid:0000149c.0000257c][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\VolumeWaitTimeMS. Using default: 20000
[07:02:58.326][tid:0000149c.0000257c][INFO] Configuration Read (DWORD): SOFTWARE\FSLogix\Profiles\DeleteLocalProfileWhenVHDShouldApply. Data: 0
[07:02:58.326][tid:0000149c.0000257c][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\FSLogixShellPath. Using default:
[07:02:58.326][tid:0000149c.0000257c][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\AccessNetworkAsComputerObject. Using default: 0
[07:02:58.326][tid:0000149c.0000257c][INFO] Accessing network as user object
[07:02:58.326][tid:0000149c.0000257c][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\AttachVHDSDDL. Using default:
[07:02:58.326][tid:0000149c.0000257c][INFO] Configuration Read (DWORD): SOFTWARE\FSLogix\Profiles\ProfileType. Data: 0
[07:02:58.326][tid:0000149c.0000257c][INFO] Profile type: Normal
[07:02:58.327][tid:0000149c.0000257c][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\CCDLocations. Using default:
[07:02:58.327][tid:0000149c.0000257c][INFO] Configuration Read (REG_SZ): SOFTWARE\FSLogix\Profiles\VHDLocations.
[07:02:58.327][tid:0000149c.0000257c][INFO] VHDLocations found – configured to use Local Disk
[07:02:58.327][tid:0000149c.0000257c][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\DiffDiskParentFolderPath. Using default: C:\Windows\TEMP\
[07:02:58.327][tid:0000149c.0000257c][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\NoProfileContainingFolder. Using default: 0
[07:02:58.327][tid:0000149c.0000257c][INFO] Configuration Read (DWORD): SOFTWARE\FSLogix\Profiles\FlipFlopProfileDirectoryName. Data: 1
[07:02:58.328][tid:0000149c.0000257c][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\VHDNameMatch. Using default: Profile*
[07:02:58.328][tid:0000149c.0000257c][INFO] Configuration Read (REG_SZ): SOFTWARE\FSLogix\Profiles\VolumeType. Data: VHDX
[07:02:58.350][tid:0000149c.0000257c][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\LockedRetryCount. Using default: 12
[07:02:58.350][tid:0000149c.0000257c][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\LockedRetryInterval. Using default: 5
[07:02:58.534][tid:0000149c.000014a0][INFO] Volume attach event
[07:02:59.390][tid:0000149c.0000257c][INFO] Detached vhd(x)
[07:02:59.392][tid:0000149c.0000257c][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\DisableRegistryLocalRedirect. Using default: 1
[07:02:59.392][tid:0000149c.0000257c][INFO] Profile VHD Path: \\viking7\fslogix\hartp_S-1-5-21-966205532-1977663930-808559644-15368\Profile_hartp.VHDX
[07:02:59.393][tid:0000149c.0000257c][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\VHDNamePattern. Using default: Profile_%username%
[07:02:59.393][tid:0000149c.0000257c][INFO] User Profile Path: C:\Users\hartp.FSL0
[07:02:59.426][tid:0000149c.000014a0][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ReAttachRetryCount. Using default: 60
[07:02:59.426][tid:0000149c.000014a0][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ReAttachIntervalSeconds. Using default: 10
[07:02:59.426][tid:0000149c.000014a0][INFO] ===== Begin Session: Volume re-attach
[07:02:59.427][tid:0000149c.000014a0][INFO] ===== End Session: Volume re-attach
[07:02:59.455][tid:0000149c.0000257c][INFO] VHD attached
[07:02:59.456][tid:0000149c.000014a0][INFO] Volume attach event
[07:02:59.535][tid:0000149c.0000257c][INFO] Volume name: \\?\Volume{b9004c21-90be-4b86-80c6-e0e36227bf0a}\
[07:02:59.540][tid:0000149c.0000257c][INFO] Profile format version 2
[07:02:59.540][tid:0000149c.0000257c][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\ProfileDirSDDL. Using default:
[07:02:59.541][tid:0000149c.0000257c][INFO] Create user directory success
[07:02:59.541][tid:0000149c.0000257c][INFO] Security looks good
[07:02:59.541][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp.FSL0 -> \\?\Volume{b9004c21-90be-4b86-80c6-e0e36227bf0a}\Profile
[07:02:59.541][tid:0000149c.0000257c][INFO] Create mount point success
[07:02:59.702][tid:0000149c.0000257c][INFO] Import Profile Registry success
[07:02:59.702][tid:0000149c.0000257c][INFO] Checking to see if cleanup necessary
[07:02:59.702][tid:0000149c.0000257c][INFO] Removing junction: C:\Users\hartp.FSL0. Adding junction C:\Users\hartp.
[07:02:59.703][tid:0000149c.0000257c][INFO] Removed redirection from C:\Users\hartp.FSL0
[07:02:59.703][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp -> \\?\Volume{b9004c21-90be-4b86-80c6-e0e36227bf0a}\Profile
[07:02:59.704][tid:0000149c.0000257c][INFO] Configuration Read (DWORD): SOFTWARE\FSLogix\Profiles\KeepLocalDir. Data: 0
[07:02:59.707][tid:0000149c.0000257c][INFO] Local temp directory: C:\Users\local_hartp
[07:02:59.707][tid:0000149c.0000257c][INFO] Configuration Read (REG_SZ): SOFTWARE\FSLogix\Profiles\RedirXMLSourceFolder. Data: \\viking7\fslogix
[07:02:59.708][tid:0000149c.0000257c][INFO] Attempting to copy: “\\viking7\fslogix\Redirections.xml” to: “C:\Users\hartp\AppData\Local\FSLogix\Redirections.xml”
[07:02:59.718][tid:0000149c.0000257c][INFO] Redirections.xml copy success
[07:02:59.718][tid:0000149c.0000257c][INFO] Reading profile folder redirections
[07:02:59.719][tid:0000149c.0000257c][INFO] Adding redirections for Credential Manager
[07:02:59.719][tid:0000149c.0000257c][INFO] Creating base folders for profile folder redirections
[07:02:59.719][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\LocalLow\Sun\Java\Deployment\security\’
[07:02:59.727][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Local\’
[07:02:59.728][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Local\AppSense\’
[07:02:59.731][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Local\CEF\’
[07:02:59.732][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Local\Adobe\’
[07:02:59.733][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Local\CrashDumps\’
[07:02:59.734][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Local\Cognos\’
[07:02:59.734][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Local\IBM\’
[07:02:59.735][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Local\Mozilla\’
[07:02:59.736][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Local\Packages\’
[07:02:59.737][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Local\ConnectedDevicePaltform\’
[07:02:59.738][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Local\Symantec\’
[07:02:59.742][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Local\Microsoft\’
[07:02:59.744][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Local\Microsoft\Teams\Current\Locales\’
[07:02:59.749][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Local\Microsoft\Teams\Packages\SquirrelTemp\’
[07:02:59.750][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Local\Microsoft\Teams\current\resources\locales\’
[07:02:59.753][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Local\SquirrelTemp\’
[07:02:59.754][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Local\Microsoft\Windows\WebCache\’
[07:02:59.761][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Local\Temp\’
[07:02:59.764][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Local\FSLogix\’
[07:02:59.765][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Local\TileDataLayer\’
[07:02:59.766][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Local\VirtualStore\’
[07:02:59.767][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\LocalLow\’
[07:02:59.767][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\LocalLow\Microsoft\’
[07:02:59.769][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\LocalLow\Adobe\’
[07:02:59.770][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Roaming\CognosRCP\’
[07:02:59.773][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Roaming\Microsoft\Signatures\’
[07:02:59.779][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Roaming\Microsoft\AppV\’
[07:02:59.781][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Roaming\Microsoft\Teams\Logs\’
[07:02:59.786][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Roaming\Microsoft\Teams\Cache\’
[07:02:59.787][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Roaming\Microsoft\Teams\Application Cache\’
[07:02:59.788][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Roaming\Microsoft\Teams\GPUCache\’
[07:02:59.790][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Roaming\Microsoft\Teams\meeting-addin\Cache\’
[07:02:59.795][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Roaming\Microsoft\Teams\Service Worker\’
[07:02:59.796][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Roaming\Microsoft\Teams\Service Worker\CacheStorage\’
[07:02:59.799][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Roaming\Microsoft\Teams\media-stack\’
[07:02:59.800][tid:0000149c.0000257c][INFO] Creating base folder ‘%USERPROFILE%\Citrix\’
[07:02:59.801][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Roaming\Microsoft\Credentials\’
[07:03:00.000][tid:0000149c.0000257c][INFO] Mirror success: C:\Users\hartp\AppData\Roaming\Microsoft\Credentials -> C:\Users\local_hartp\AppData\Roaming\Microsoft\Credentials
[07:03:00.000][tid:0000149c.0000257c][INFO] Creating base folder ‘AppData\Local\Microsoft\Credentials\’
[07:03:00.204][tid:0000149c.0000257c][INFO] Mirror success: C:\Users\hartp\AppData\Local\Microsoft\Credentials -> C:\Users\local_hartp\AppData\Local\Microsoft\Credentials
[07:03:00.204][tid:0000149c.0000257c][INFO] Adding include rule for folder ‘AppData\LocalLow\Sun\Java\Deployment\security\’
[07:03:00.205][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\LocalLow\Sun\Java\Deployment\security -> \??\Volume{b9004c21-90be-4b86-80c6-e0e36227bf0a}\Profile\AppData\LocalLow\Sun\Java\Deployment\security
[07:03:00.205][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Local\’
[07:03:00.205][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Local -> C:\Users\local_hartp\AppData\Local
[07:03:00.205][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Local\AppSense\’
[07:03:00.205][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Local\AppSense -> C:\Users\local_hartp\AppData\Local\AppSense
[07:03:00.205][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Local\CEF\’
[07:03:00.205][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Local\CEF -> C:\Users\local_hartp\AppData\Local\CEF
[07:03:00.205][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Local\Adobe\’
[07:03:00.205][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Local\Adobe -> C:\Users\local_hartp\AppData\Local\Adobe
[07:03:00.205][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Local\CrashDumps\’
[07:03:00.205][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Local\CrashDumps -> C:\Users\local_hartp\AppData\Local\CrashDumps
[07:03:00.205][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Local\Cognos\’
[07:03:00.205][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Local\Cognos -> C:\Users\local_hartp\AppData\Local\Cognos
[07:03:00.205][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Local\IBM\’
[07:03:00.205][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Local\IBM -> C:\Users\local_hartp\AppData\Local\IBM
[07:03:00.205][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Local\Mozilla\’
[07:03:00.205][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Local\Mozilla -> C:\Users\local_hartp\AppData\Local\Mozilla
[07:03:00.205][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Local\Packages\’
[07:03:00.205][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Local\Packages -> C:\Users\local_hartp\AppData\Local\Packages
[07:03:00.205][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Local\ConnectedDevicePaltform\’
[07:03:00.205][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Local\ConnectedDevicePaltform -> C:\Users\local_hartp\AppData\Local\ConnectedDevicePaltform
[07:03:00.205][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Local\Symantec\’
[07:03:00.205][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Local\Symantec -> C:\Users\local_hartp\AppData\Local\Symantec
[07:03:00.205][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Local\Microsoft\’
[07:03:00.205][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Local\Microsoft -> C:\Users\local_hartp\AppData\Local\Microsoft
[07:03:00.205][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Local\Microsoft\Teams\Current\Locales\’
[07:03:00.205][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Local\Microsoft\Teams\Current\Locales -> C:\Users\local_hartp\AppData\Local\Microsoft\Teams\Current\Locales
[07:03:00.205][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Local\Microsoft\Teams\Packages\SquirrelTemp\’
[07:03:00.206][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Local\Microsoft\Teams\Packages\SquirrelTemp -> C:\Users\local_hartp\AppData\Local\Microsoft\Teams\Packages\SquirrelTemp
[07:03:00.206][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Local\Microsoft\Teams\current\resources\locales\’
[07:03:00.206][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Local\Microsoft\Teams\current\resources\locales -> C:\Users\local_hartp\AppData\Local\Microsoft\Teams\current\resources\locales
[07:03:00.206][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Local\SquirrelTemp\’
[07:03:00.206][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Local\SquirrelTemp -> C:\Users\local_hartp\AppData\Local\SquirrelTemp
[07:03:00.206][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Local\Microsoft\Windows\WebCache\’
[07:03:00.206][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Local\Microsoft\Windows\WebCache -> C:\Users\local_hartp\AppData\Local\Microsoft\Windows\WebCache
[07:03:00.206][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Local\Temp\’
[07:03:00.206][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Local\Temp -> C:\Users\local_hartp\AppData\Local\Temp
[07:03:00.206][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Local\FSLogix\’
[07:03:00.206][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Local\FSLogix -> C:\Users\local_hartp\AppData\Local\FSLogix
[07:03:00.206][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Local\TileDataLayer\’
[07:03:00.206][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Local\TileDataLayer -> C:\Users\local_hartp\AppData\Local\TileDataLayer
[07:03:00.206][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Local\VirtualStore\’
[07:03:00.206][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Local\VirtualStore -> C:\Users\local_hartp\AppData\Local\VirtualStore
[07:03:00.206][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\LocalLow\’
[07:03:00.206][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\LocalLow -> C:\Users\local_hartp\AppData\LocalLow
[07:03:00.206][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\LocalLow\Microsoft\’
[07:03:00.206][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\LocalLow\Microsoft -> C:\Users\local_hartp\AppData\LocalLow\Microsoft
[07:03:00.206][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\LocalLow\Adobe\’
[07:03:00.206][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\LocalLow\Adobe -> C:\Users\local_hartp\AppData\LocalLow\Adobe
[07:03:00.206][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Roaming\CognosRCP\’
[07:03:00.206][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Roaming\CognosRCP -> C:\Users\local_hartp\AppData\Roaming\CognosRCP
[07:03:00.206][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Roaming\Microsoft\Signatures\’
[07:03:00.206][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Roaming\Microsoft\Signatures -> C:\Users\local_hartp\AppData\Roaming\Microsoft\Signatures
[07:03:00.206][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Roaming\Microsoft\AppV\’
[07:03:00.206][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Roaming\Microsoft\AppV -> C:\Users\local_hartp\AppData\Roaming\Microsoft\AppV
[07:03:00.206][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Roaming\Microsoft\Teams\Logs\’
[07:03:00.206][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Roaming\Microsoft\Teams\Logs -> C:\Users\local_hartp\AppData\Roaming\Microsoft\Teams\Logs
[07:03:00.206][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Roaming\Microsoft\Teams\Cache\’
[07:03:00.207][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Roaming\Microsoft\Teams\Cache -> C:\Users\local_hartp\AppData\Roaming\Microsoft\Teams\Cache
[07:03:00.207][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Roaming\Microsoft\Teams\Application Cache\’
[07:03:00.207][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Roaming\Microsoft\Teams\Application Cache -> C:\Users\local_hartp\AppData\Roaming\Microsoft\Teams\Application Cache
[07:03:00.207][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Roaming\Microsoft\Teams\GPUCache\’
[07:03:00.207][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Roaming\Microsoft\Teams\GPUCache -> C:\Users\local_hartp\AppData\Roaming\Microsoft\Teams\GPUCache
[07:03:00.207][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Roaming\Microsoft\Teams\meeting-addin\Cache\’
[07:03:00.207][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Roaming\Microsoft\Teams\meeting-addin\Cache -> C:\Users\local_hartp\AppData\Roaming\Microsoft\Teams\meeting-addin\Cache
[07:03:00.207][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Roaming\Microsoft\Teams\Service Worker\’
[07:03:00.207][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Roaming\Microsoft\Teams\Service Worker -> C:\Users\local_hartp\AppData\Roaming\Microsoft\Teams\Service Worker
[07:03:00.207][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Roaming\Microsoft\Teams\Service Worker\CacheStorage\’
[07:03:00.207][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Roaming\Microsoft\Teams\Service Worker\CacheStorage -> C:\Users\local_hartp\AppData\Roaming\Microsoft\Teams\Service Worker\CacheStorage
[07:03:00.207][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Roaming\Microsoft\Teams\media-stack\’
[07:03:00.207][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Roaming\Microsoft\Teams\media-stack -> C:\Users\local_hartp\AppData\Roaming\Microsoft\Teams\media-stack
[07:03:00.207][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘%USERPROFILE%\Citrix\’
[07:03:00.207][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\%USERPROFILE%\Citrix -> C:\Users\local_hartp\%USERPROFILE%\Citrix
[07:03:00.207][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Roaming\Microsoft\Credentials\’
[07:03:00.207][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Roaming\Microsoft\Credentials -> C:\Users\local_hartp\AppData\Roaming\Microsoft\Credentials
[07:03:00.207][tid:0000149c.0000257c][INFO] Adding exclude rule for folder ‘AppData\Local\Microsoft\Credentials\’
[07:03:00.207][tid:0000149c.0000257c][INFO] Added redirection C:\Users\hartp\AppData\Local\Microsoft\Credentials -> C:\Users\local_hartp\AppData\Local\Microsoft\Credentials
[07:03:00.207][tid:0000149c.0000257c][INFO] Folder redirections created
[07:03:00.207][tid:0000149c.0000257c][INFO] Status set to 0: Success
[07:03:00.209][tid:0000149c.0000257c][INFO] Profile refcount incremented to: 1
[07:03:00.209][tid:0000149c.0000257c][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\CleanOutNotifications. Using default: 1
[07:03:00.209][tid:0000149c.0000257c][INFO] Prep1
[07:03:00.212][tid:0000149c.0000257c][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\RegisterAppNotifications. Using default: 1
[07:03:00.212][tid:0000149c.0000257c][INFO] Prep2
[07:03:00.212][tid:0000149c.0000257c][INFO] Prep2 C:\Users\hartp\AppData\Local\Microsoft\Windows\UsrClass.dat was not found.
[07:03:00.212][tid:0000149c.0000257c][INFO] OneDriveTemp setup
[07:03:00.212][tid:0000149c.0000257c][INFO] C:\OneDriveTemp\S-1-5-21-966205532-1977663930-808559644-15368 –> \\?\Volume{b9004c21-90be-4b86-80c6-e0e36227bf0a}\ODTemp
[07:03:00.212][tid:0000149c.0000257c][INFO] OneDriveTemp setup successful
[07:03:00.212][tid:0000149c.0000257c][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\PreventLoginWithFailure. Using default: 0
[07:03:00.216][tid:0000149c.0000257c][INFO] vhd(x) \\viking7\fslogix\hartp_S-1-5-21-966205532-1977663930-808559644-15368\Profile_hartp.VHDX has 29829.92 MB left (99.44 % free)
[07:03:00.216][tid:0000149c.0000257c][INFO] LoadProfile successful. User: hartp. SID: S-1-5-21-966205532-1977663930-808559644-15368.
[07:03:00.216][tid:0000149c.0000257c][INFO] loadProfile time: 1890 milliseconds
[07:03:00.217][tid:0000149c.0000257c][INFO] ===== End Session: LoadProfile: hartp
[07:03:00.217][tid:0000149c.0000257c][INFO] ===== End Session: Logon
[07:07:14.349][tid:0000149c.0000257c][INFO] ===== Begin Session: StartShell
[07:07:14.350][tid:0000149c.0000257c][INFO] User: S-1-5-21-966205532-1977663930-808559644-15368 (hartp)
[07:07:14.350][tid:0000149c.0000257c][INFO] Acquiring mutex for user logon
[07:07:14.350][tid:0000149c.0000257c][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\LogonSyncMutexTimeout. Using default: 60000
[07:07:14.350][tid:0000149c.0000257c][INFO] Mutex acquired
[07:07:14.370][tid:0000149c.0000257c][INFO] ===== Begin Session: Logon notification: hartp
[07:07:14.370][tid:0000149c.0000257c][INFO] Session configuration read (REG_SZ): SOFTWARE\FSLogix\Profiles\Sessions\S-1-5-21-966205532-1977663930-808559644-15368\ActivityId = ‘e5682adc-978c-0000-dee7-68e58c97d601’
[07:07:14.370][tid:0000149c.0000257c][INFO] Configuration Read (DWORD): SOFTWARE\FSLogix\Profiles\ConcurrentUserSessions. Data: 1
[07:07:14.370][tid:0000149c.0000257c][INFO] Checking Profile Data Export for S-1-5-21-966205532-1977663930-808559644-15368
[07:07:14.379][tid:0000149c.0000257c][INFO] Configuration Read (DWORD): SOFTWARE\FSLogix\Profiles\SetTempToLocalPath. Data: 3
[07:07:14.379][tid:0000149c.0000257c][INFO] Initiating set up of TMP and TEMP environment variables to local disk
[07:07:14.379][tid:0000149c.0000257c][INFO] Creating temp directory: C:\Users\local_hartp\Temp
[07:07:14.380][tid:0000149c.0000257c][INFO] Directory already exists
[07:07:14.380][tid:0000149c.0000257c][INFO] Setting TMP and TEMP registry entries to: C:\Users\local_hartp\Temp
[07:07:14.380][tid:0000149c.0000257c][INFO] Setting INetCache folder
[07:07:14.418][tid:0000149c.0000257c][INFO] INetCache folder successfully changed
[07:07:14.692][tid:0000149c.0000257c][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\OutlookCachedMode. Using default: 1
[07:07:14.693][tid:0000149c.0000257c][INFO] Outlook cached mode policy rule added
[07:07:14.693][tid:0000149c.0000257c][INFO] Configuration Read (DWORD): SOFTWARE\FSLogix\Apps\RoamSearch. Data: 2
[07:07:14.693][tid:0000149c.0000257c][INFO] Configuration Read (DWORD): SOFTWARE\Policies\FSLogix\ODFC\RoamSearch. Data: 2
[07:07:14.693][tid:0000149c.0000257c][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\RoamSearch. Using default: 0
[07:07:14.693][tid:0000149c.0000257c][INFO] WindowsSearchModule is not started. ‘RoamSearch’ was not set on service start.
[07:07:14.693][tid:0000149c.0000257c][INFO] Configuration setting not found: SOFTWARE\FSLogix\Profiles\EnableSpecialRoamingProfile. Using default: 0
[07:07:14.702][tid:0000149c.0000257c][INFO] ===== End Session: Logon notification: hartp
[07:07:14.935][tid:0000149c.000014a0][INFO] Volume attach event
[07:07:15.341][tid:0000149c.0000257c][INFO] ===== End Session: StartShell
That looks like a successful logon. Are there any errors logged when the lock actually happens and the logon fails?
Hi james, we also face similar issue whenver weupdate the template and push the chamges to VDI the first login after restart user are not able to load the vhdfiles.. The mousecursor will revolve for 10 to 15minutes and it will show c:\windows\users\%userid%\desktop not found.
Hello James,
in Server 2019 with GPO Caching enabled, the FileSys Path of the cached GPOs is:
C:\ProgramData\Microsoft\GroupPolicy\Users\S-1-5-21-587364077-1479819389-837300805-21126\DataStore\0\sysvol\…
Can you confirm? The “GroupPolicyState = 0” does not help.
Thanks.
Hi
I haven’t noticed that but we are still pretty much on 2016. Will check when I get a minute.
Hi James
Ha. Excellent find, thank you!
Cheers
AJAL
I have a question: How do you decide what goes into the redir.xml file?
Reason I ask is cos I am only excluding Teams folders but I am seeing a lot of LRS Hot writes into the profiles and I cannot find a way to track down what is writing so much?
How do you decide? You observe the performance of the system and decided what shouldn’t go in there, usually.
When you say “LRS Hot Writes”, what do you mean?
Hi James,
If RedirXML file is not configured but the Event ID 1086 and error description “can not complete this function is present” would you suggest removing the HK keys ?
Is this specifically a GP issue you are seeing?
Hi. We seem to be having a weird issue in that when we create a registry group policy preferences that references the HKCU\Software\Microsoft\Office key, it’s not being applied at logon. You can run gpupdate and it then gets applied, but we can’t expect our users to be doing that. Any idea waht the issue might be? It’s only that key.
Is this an FSLogix issue? Or GP in general?
Sorry. I should have been more clear on this. We are using FSLogix for both O365 and Profile containers
https://social.msdn.microsoft.com/Forums/en-US/eb13e600-a68a-4059-902c-5588e8b9d85f/registry-preference-policies-not-applying-to-office-key?forum=FSLogix
This pretty much sums up the issue
Sounds like FSLogix is overwriting the Registry preference keys. What happens if you set them via a Scheduled Task that runs at logon?
Don’t know. Haven’t thought of or tried that. I’ll give it a go. I’ve also logged a call with MS about it, but just wondering if it’s something anyone else was experiencing? Thanks for your help James
We logged a call with MS about this and the fix, at least for us, was to create the registry key:
HKLM\Software\Policies\FSLogix\ODFC
“RefreshUserPolicy”=dword:00000001
Hope it helps if anyone else having the same issue
Hi James,
I have a question about what you have posted above. You mentioned, “There is also a setting in the same folder called Configure Group Policy Caching, but this seems to only apply to clients where it should be on by default anyway.” I’ve noticed other individuals comment to Disable the “Configure Group Policy Caching” and was just curious if that is outdated information before Citrix LTSR 1912 or CR?
As far as I am aware this only applies to “client” operating systems, so it should be on by default anyway and does not apply to Server.
Hi James,
thanks for your great work. Do you know if the Problem still exists with current Version of FSLogix?
On my Customers Side I run in the same issue like your baseline article.
Also strange, with citrix profile container everything is working fine.
Yes, it still exists because it’s not really a problem, it’s a misconfiguration by the administrator (excluding things that shouldn’t be excluded).