Do you want to customize your Windows context menus with File Explorer functions? Read on…
I had a request recently where users on a single image wanted to add customized context menu (right-click menu) functions for specific Active Directory groups. There are certain functions within Explorer that are either listed as buttons in the File Explorer interface, or only exposed by performing certain actions (such as holding down Shift, or clicking through other menus).
The actual request was for developers to have access to the Run As A Different User and Advanced Security features from the context menu.
Details
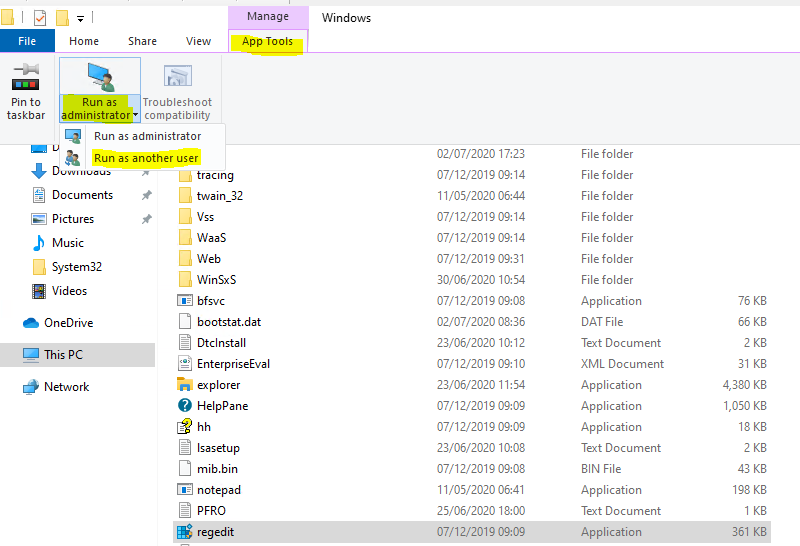
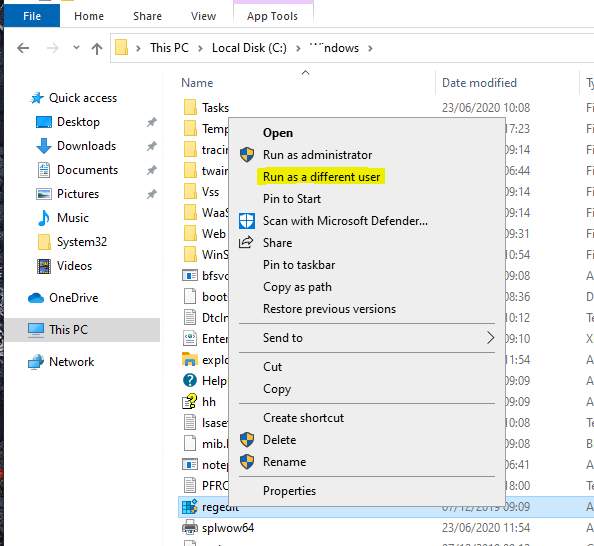
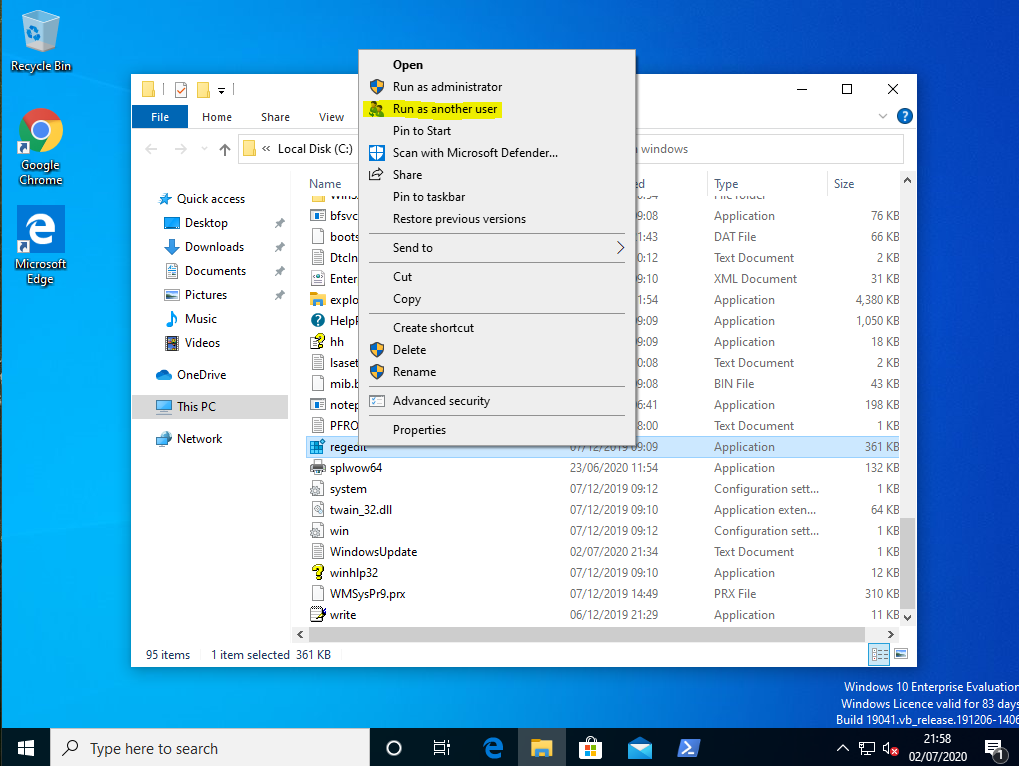
Currently, if you want to access Run As A Different User you have to hold <Shift> and right-click at the same time – a bit fiddly. Alternatively, you can highlight the file you want to run in File Explorer, click the Manage tab on the ribbon which has App Tools on it, click the drop-down next to Run as administrator, and choose Run as another user. One of these options is fiddly, the other, long-winded – hence the first request to move it to the context menu for users that have to do it a lot.
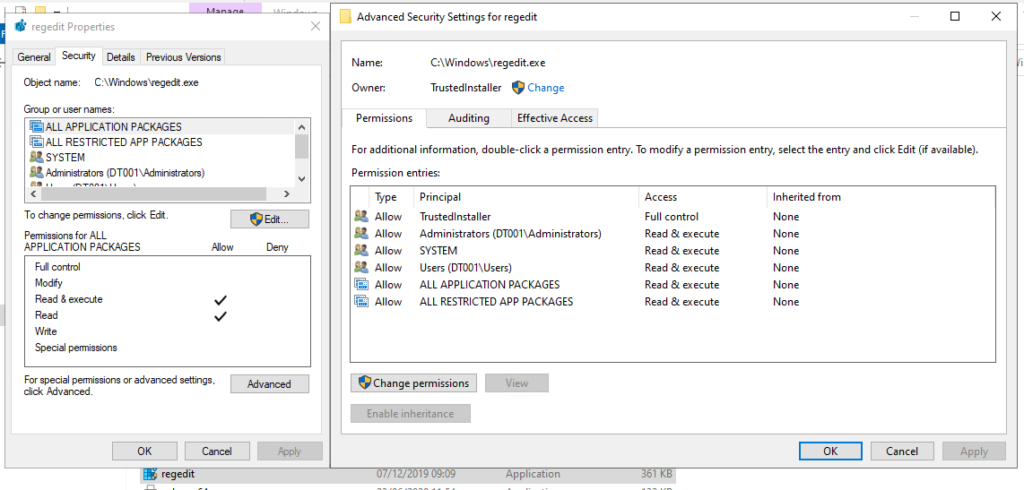
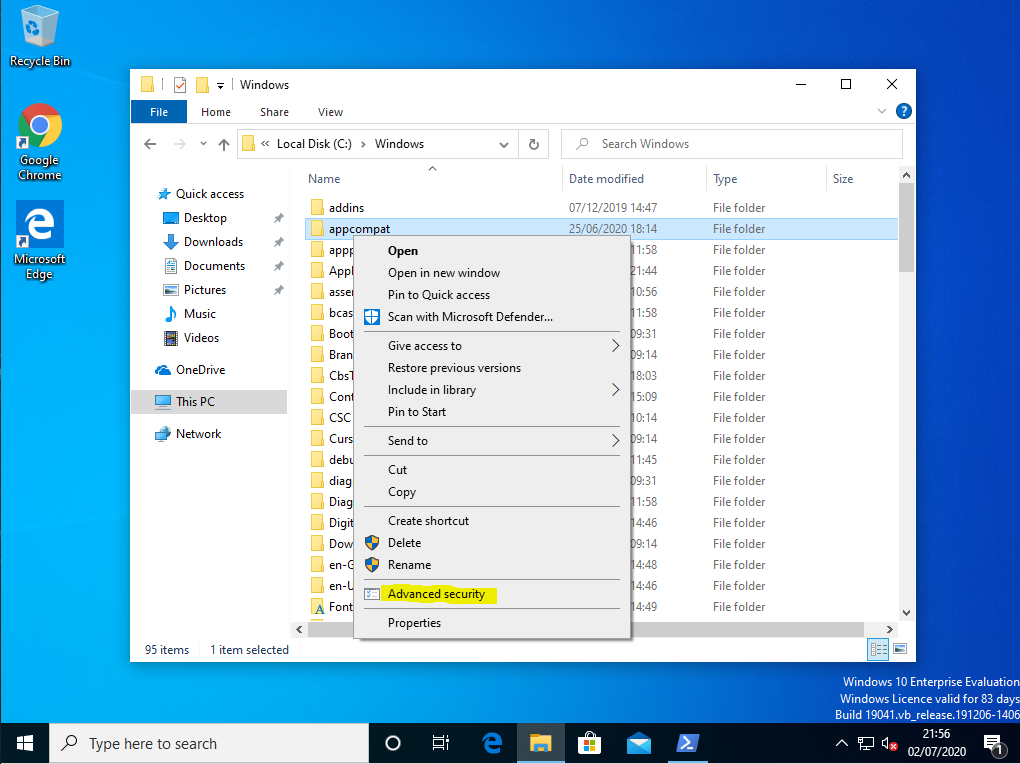
The Advanced Security page is even more annoyingly fiddly. Firstly, you can right-click the target file or folder, choose the Security tab, and click on Advanced. Alternatively, you can highlight the file or folder in File Explorer, click on the Share tab in the ribbon, and click Advanced Security. Again, both of these are not particularly intuitive or lend themselves to easy access.

Solution
It’s not particularly hard to transfer Windows File Explorer functions into context menu items – you just need to know where to look in the Registry. The first part of copying them to the context menu is locating the existing functions.
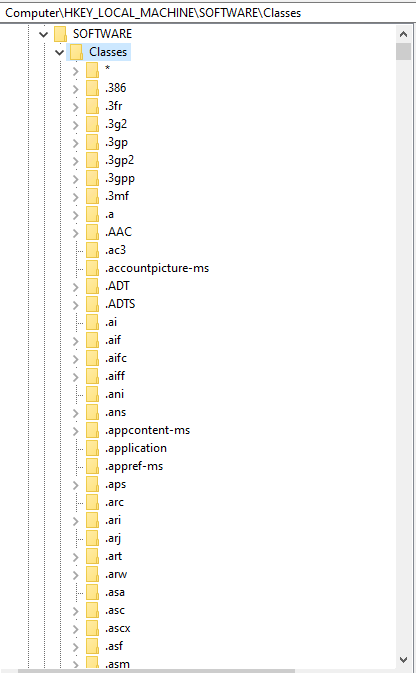
Virtually every button function you see in File Explorer in Windows 10 maps to a part of the Registry. The key you are interested in is this one:-
HKLM\Software\Microsoft\Windows\CurrentVersion\Explorer\CommandStore\shellEvery subkey in here refers to functions you normally see available within the File Explorer window, although the availability of some of them depend on what you are working with in the view. Some of them seem pretty intuitive, others are a bit more vague. You will need to experiment with them a bit on occasion to try and find the one you are after, so it always pays to take a snapshot of the machine you are doing the discovery on!
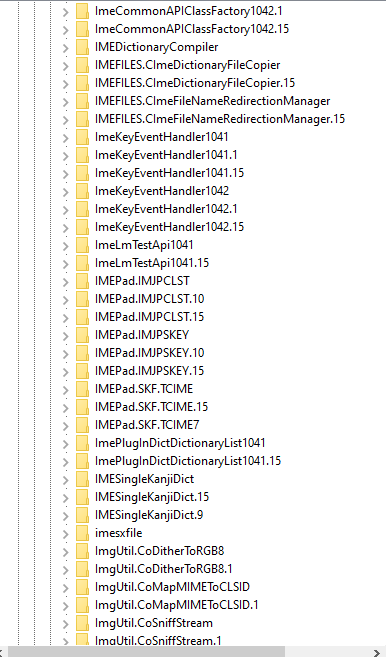
I am looking for the Run As A Different User function in the first instance, and this one is pretty obvious:-
Windows.runasuserThe second one – Advanced Security – was a lot less obvious. Eventually, some trial and error and a spot of Googling allowed me to find it:-
Windows.RibbonPermissionsDialogOnce you’re armed with the subkey names, we can move on to switching these to context menu items.
HKEY_CLASSES_ROOT is the area of the Registry that we’re commonly told deals with context menu items (amongst many other things). However, if you’re switched on you will already know that HKCR is simply an amalgamation of HKCU and HKLM settings. The two keys that feed into HKCR are
HKLM\Software\Classes
HKCU\Software\ClassesSo we can use HKLM if we want the new items to appear on a device level (so for all users on the device), and use HKCU if we just want to target the new items to specific users or groups of users.
Underneath the Software\Classes key are other subkeys that define when these new context menu items will appear. So dependent on what you put here, this will tell you what items you need to right-click on to see the new menu entries.
If you put the new items in Software\Classes\*\shell, they will appear for ALL FILES
If you put the new items in Software\Classes\Directory\shell, they will appear for ALL FOLDERS
If you put the new items in Software\Classes\AllFileSystemObjects\shell, they will appear for ALL FILES AND FOLDERS
You can also specify particular file extensions or file types, which is useful for functions like Run As A Different User which only really applies to executable files. The list of filetypes and file extensions appears for the most part under HKLM\Software\Classes and you can see there are literally thousands you can choose from. For instance, functions like “Set as background” are (obviously) only applied to image files.
It’s important to take stock at this stage and decide with which items you want your new context menu entries to appear. However, if you get it wrong, it generally won’t cause too many issues – for instance, if you try to “Run As A Different User” on a folder rather than an executable file, it throws an error and then exits. Like I said though, this is why snapshots are important! 🙂
For my purposes, I have decided that Run As A Different User will be associated with all executable filetypes, and Advanced Security will be associated with all files and folders. As far as I can tell, executables should be covered by the following filetypes:-
exefile
batfile
cmdfile
MSI.Package
mscfileSo now we need to transfer the entries from the Registry keys we identified into the context menu subkeys. However, as we are doing them for a specific group of users, we want to import them into the HKCU area. Whether you are exporting to HKLM or HKCU, the easiest way to do this is to export out a REG file and then import it into Group Policy Preferences.
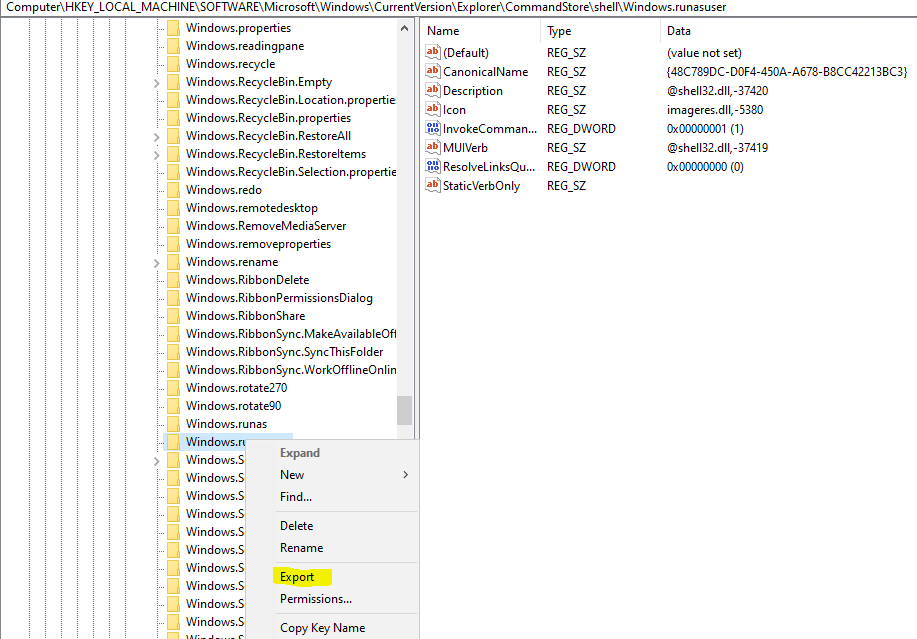
Target the keys you identified from HKLM\Software\Microsoft\Windows\CurrentVersion\Explorer\CommandStore\shell and export all of them to .reg files by right-clicking on the key and choosing Export. Save the .reg files for as many keys as you are dealing with
Once you have saved the .reg files, you need to edit them to apply them to the target areas you want. In my first .reg file (the one for Run As A Different User), I will substitute the paths in the .reg file like this
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\CommandStore is replaced with HKEY_CURRENT_USER\Software\Classes\filetype
So the reg file below that we exported
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\CommandStore\shell\Windows.runasuser]
"CanonicalName"="{48C789DC-D0F4-450A-A678-B8CC42213BC3}"
"Description"="@shell32.dll,-37420"
"Icon"="imageres.dll,-5380"
"InvokeCommandOnSelection"=dword:00000001
"MUIVerb"="@shell32.dll,-37419"
"ResolveLinksQueryBehavior"=dword:00000000
"StaticVerbOnly"=""Is edited to this, with five replacements matching up to the five filetypes we identified
Windows Registry Editor Version 5.00
[HKEY_CURRENT_USER\Software\Classes\exefile\shell\Windows.runasuser]
"CanonicalName"="{48C789DC-D0F4-450A-A678-B8CC42213BC3}"
"Description"="@shell32.dll,-37420"
"Icon"="imageres.dll,-5380"
"InvokeCommandOnSelection"=dword:00000001
"MUIVerb"="@shell32.dll,-37419"
"ResolveLinksQueryBehavior"=dword:00000000
"StaticVerbOnly"=""
[HKEY_CURRENT_USER\Software\Classes\batfile\shell\Windows.runasuser]
"CanonicalName"="{48C789DC-D0F4-450A-A678-B8CC42213BC3}"
"Description"="@shell32.dll,-37420"
"Icon"="imageres.dll,-5380"
"InvokeCommandOnSelection"=dword:00000001
"MUIVerb"="@shell32.dll,-37419"
"ResolveLinksQueryBehavior"=dword:00000000
"StaticVerbOnly"=""
[HKEY_CURRENT_USER\Software\Classes\cmdfile\shell\Windows.runasuser]
"CanonicalName"="{48C789DC-D0F4-450A-A678-B8CC42213BC3}"
"Description"="@shell32.dll,-37420"
"Icon"="imageres.dll,-5380"
"InvokeCommandOnSelection"=dword:00000001
"MUIVerb"="@shell32.dll,-37419"
"ResolveLinksQueryBehavior"=dword:00000000
"StaticVerbOnly"=""
[HKEY_CURRENT_USER\Software\Classes\mscfile\shell\Windows.runasuser]
"CanonicalName"="{48C789DC-D0F4-450A-A678-B8CC42213BC3}"
"Description"="@shell32.dll,-37420"
"Icon"="imageres.dll,-5380"
"InvokeCommandOnSelection"=dword:00000001
"MUIVerb"="@shell32.dll,-37419"
"ResolveLinksQueryBehavior"=dword:00000000
"StaticVerbOnly"=""
[HKEY_CURRENT_USER\Software\Classes\MSI.Package\shell\Windows.runasuser]
"CanonicalName"="{48C789DC-D0F4-450A-A678-B8CC42213BC3}"
"Description"="@shell32.dll,-37420"
"Icon"="imageres.dll,-5380"
"InvokeCommandOnSelection"=dword:00000001
"MUIVerb"="@shell32.dll,-37419"
"ResolveLinksQueryBehavior"=dword:00000000
"StaticVerbOnly"=""Next we take the exported .reg file we made for Advanced Security which looks like this
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\CommandStore\shell\Windows.RibbonPermissionsDialog]
"CommandStateSync"=""
"ExplorerCommandHandler"="{E2765AC3-564C-40F9-AC12-CD393FBAAB0F}"This time we simply need to apply it to ALL FILES AND FOLDERS, so we only need replace HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\CommandStore with HKEY_CURRENT_USER\Software\Classes\AllFileSystemObjects as below
Windows Registry Editor Version 5.00
[HKEY_CURRENT_USER\Software\Classes\AllFileSystemObjects\shell\Windows.RibbonPermissionsDialog]
"CommandStateSync"=""
"ExplorerCommandHandler"="{E2765AC3-564C-40F9-AC12-CD393FBAAB0F}"You can also optionally add bits to these .reg files to tell them what icon to show on the context menu and where to place it. For instance, if you add the following text to the end of the Advanced Security .reg file…
"Icon"="ntshrui.dll,4"
"Position"="Bottom"…it will give it the correct icon and move it to the bottom of the menu. Looking up icons is a fiddly business – IconsExtract from NirSoft can help you find them if you’re into that sort of thing.
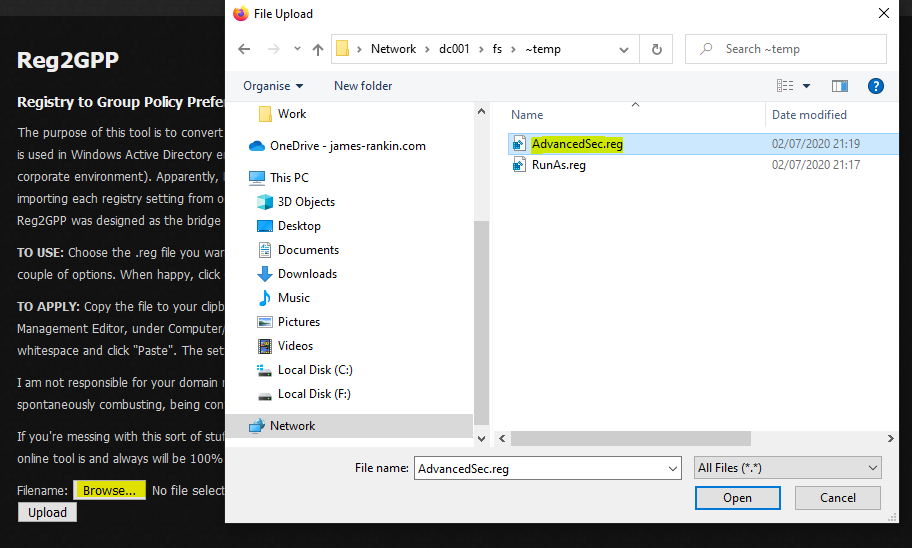
Once you’ve completed your edited .reg files, you need to somehow deploy them into the machine (if they’re HKLM entries) or into the user session (for HKCU entries). I find the easiest way to do this is via Group Policy Preferences, but you could do it any number of other ways (Citrix WEM, Ivanti UWM, a script, PolicyPak, etc.)
However, it is a bit non-trivial to easily convert .reg files into XML files for easy import into GPP – unless you go digging about on the internet. I found a site which actually lets you upload your .reg files and spits out an XML file you can use straight in GPP – https://www.runecasters.com.au/reg2gpp. It may look very dated, but the functionality still works. Simply click Browse, select the .reg file you edited, and click Upload.
Next, just select the options you want (I always use Replace to ensure it is enforced, and if it is an HKCU setting I use “run in logged-on user’s context”) and then click the Convert and Download button
Once you’ve done this for all your .reg files, switch across to Group Policy Management and create a GPO. Go to User (or Computer) Configuration | Preferences | Windows Settings | Registry. Now, open up the XML file you saved (in Notepad will be fine), and copy the text from it

Now, simply go back to the Registry window of your Group Policy Object, and just right-click and choose Paste.
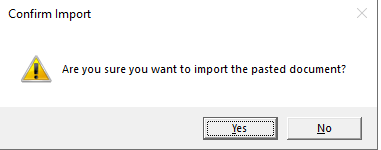
Click on Yes on the confirmation dialog
Hey presto – you should have a ready-made GPP with all of your Registry settings imported straight in!

Repeat this as many times as you need to for each XML file you created

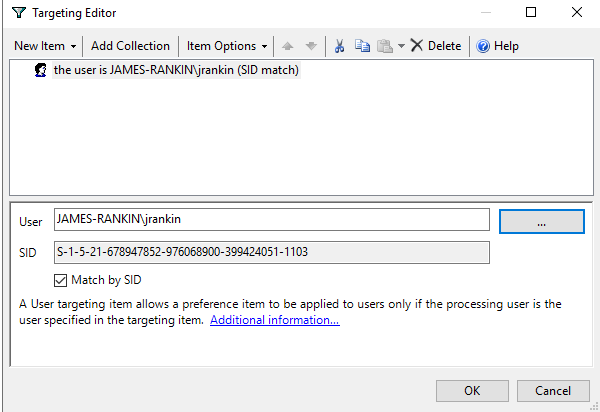
Finally, you can optionally use Item-Level Targeting on each setting (you can do it at the root of the collection and it will apply to all the subfolders) so that it is only applied to specific users and groups, if necessary
Now, once this is applied to your target devices, you should see that when a user logs on from the target groups (or simply to the target device if you have applied the settings at an HKLM level), you will have the new context menus applied.
Summary
So there you go, it just a case of doing some Registry sleuthing to allow yourself to add the functions from File Explorer into the Windows right-click context menu. This is handy for allowing users to access configuration items more quickly if they use these particular features a lot.
Obviously, always take care when digging around in the guts of the Registry, and make sure you take snapshots!
Underneath is a YouTube video of the process to show you how it works.